With cyber threats becoming increasingly sophisticated, it is crucial to implement robust security measures to protect sensitive information. This is where SOC 2 compliance software comes into play. We will take a closer look at how this software can help organizations achieve SOC 2 compliance, highlight SOC 2 compliance vendors, and emphasize why Compliancy Group ultimately stands out as the best option in the field.
Understanding SOC 2 Compliance
SOC 2 (System and Organization Controls) is an essential framework developed by the American Institute of CPAs (AICPA) that focuses on customer data:
- Security
- Availability
- Processing Integrity
- Confidentiality
- Privacy
It sets a high standard for service providers to ensure proper controls are in place to safeguard protected health information (PHI).
To achieve SOC 2 compliance, organizations must demonstrate that they have implemented comprehensive policies and procedures aligning with the five trust principles mentioned above. They must also undergo rigorous audits conducted by certified professionals who assess their adherence to these standards.
Key Features of SOC 2 Compliance Software
SOC 2 compliance software simplifies the process of achieving and maintaining compliance by providing organizations with a centralized platform to manage their security controls effectively. It offers a range of features designed specifically to address SOC 2 requirements while streamlining internal processes.
1. Risk Assessment & Management
Risk assessment and management is a crucial process that helps organizations identify potential vulnerabilities and risks, prioritize them based on severity and likelihood, and allocate resources efficiently to mitigate the identified risks.
2. Streamlined Process
SOC 2 compliance software provides a structured approach to guide organizations through each step of the compliance journey. It streamlines the process by automating tasks, saving time and effort.
3. Comprehensive Security Controls
SOC 2 compliance software ensures that all necessary security controls are in place to meet SOC 2 requirements. It helps identify gaps, provides recommendations for improvement, and tracks progress toward compliance.
4. Ongoing Monitoring
SOC 2 compliance is not a one-time achievement; it requires continuous monitoring and updates. Compliance software enables organizations to assess their security posture regularly, detect deviations from established controls, and take corrective actions promptly.
5. Documentation Management
SOC 2 compliance involves maintaining detailed documentation to demonstrate adherence to the required standards. SOC 2 compliance software simplifies this process by offering centralized document management capabilities.
SOC 2 Compliance Vendors: Safeguarding Your Data
SOC 2 compliance vendors are third-party service providers that assist organizations in achieving and maintaining SOC 2 compliance. These vendors offer a range of services, including:
- Audit Preparation
- Risk Assessment
- Policy & Procedure Development
- Ongoing Monitoring
They have extensive knowledge and expertise in the field of data security and privacy regulations, as well as the specific requirements outlined in the SOC 2 framework. By partnering with SOC 2 compliance vendors, businesses can:
- Streamline their compliance efforts
- Ensure adherence to industry best practices
- Demonstrate commitment to protecting customer data
SOC 2 compliance vendors provide valuable guidance and support throughout the compliance process, helping organizations meet their obligations and build trust with their stakeholders.
Compliancy Group: The Best SOC 2 Compliance Software
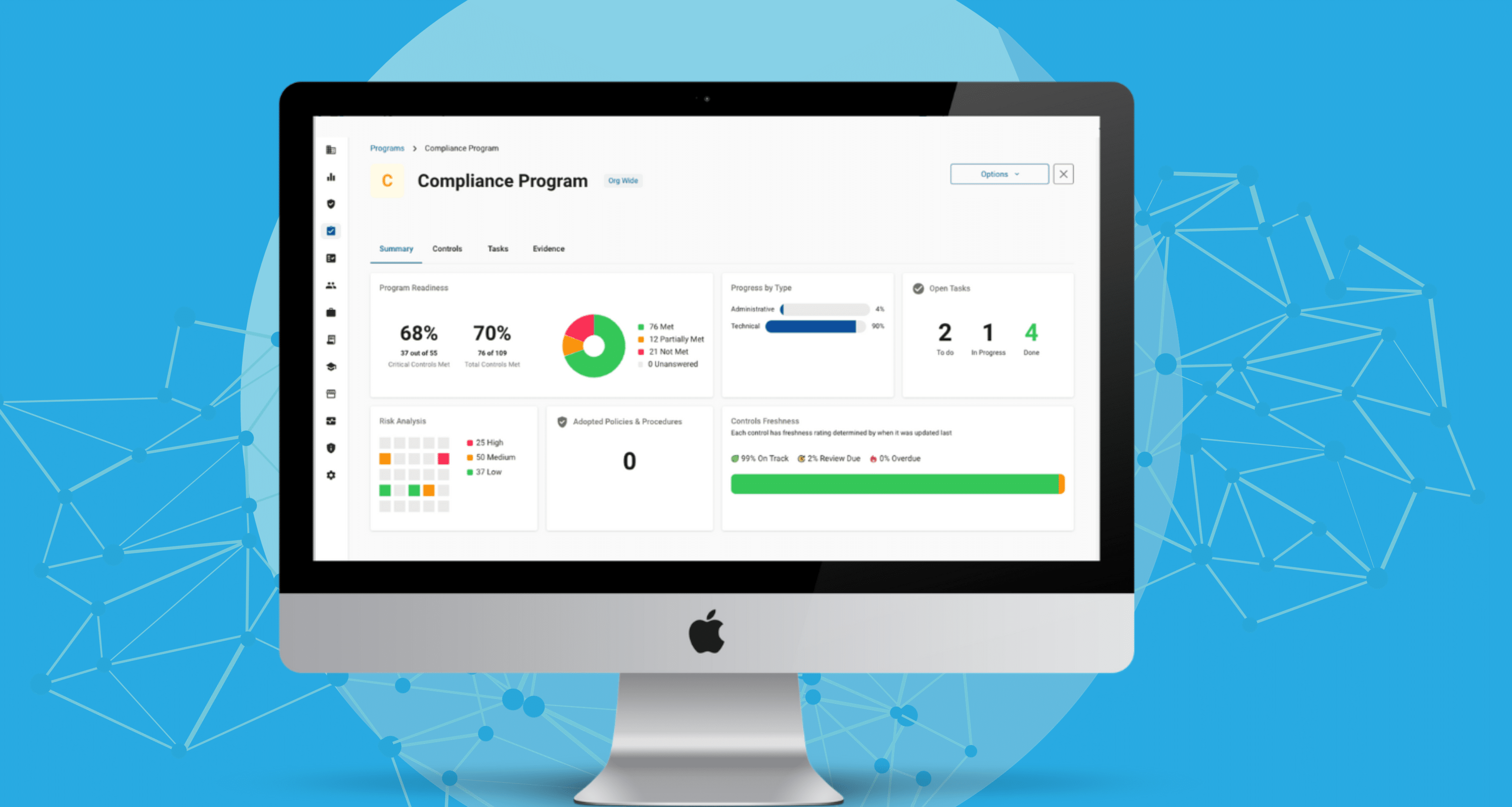
Compliancy Group stands out as the best software solution to prepare healthcare organizations for a SOC 2 audit. With its robust features and comprehensive approach, Compliancy Group ensures organizations are fully prepared for the rigorous SOC 2 requirements. Through their readiness capabilities, this software empowers businesses to assess, enhance, and maintain their security controls effectively.
By providing a step-by-step process to enable businesses to meet all SOC 2 criteria, Compliancy Group’s software simplifies the compliance journey and minimizes the risk of non-compliance. Their innovative tools offer continuous monitoring, remediation assistance, and documentation management, allowing organizations to demonstrate ongoing adherence to SOC 2 standards. Overall, Compliancy Group’s SOC 2 readiness software is unmatched in its ability to help businesses achieve and maintain compliance efficiently and successfully.








