In today’s digital landscape, data security is of utmost importance. With the ever-increasing number of cyber threats, organizations must take proactive measures to protect sensitive information and maintain the trust of their customers. One such measure is SOC 2 compliance, a widely recognized standard that demonstrates an organization’s commitment to safeguarding data.
What is SOC 2 Compliance?
SOC 2 compliance refers to adhering to the Service Organization Control (SOC) 2 framework established by the American Institute of Certified Public Accountants (AICPA). It focuses on the security, availability, processing integrity, confidentiality, and privacy of customer data held by service providers.
The Importance of SOC 2 Compliance: Safeguarding Your Business
Maintaining SOC 2 compliance is crucial for businesses that store or process customer data in the cloud or any other third-party systems. By achieving SOC 2 compliance, organizations demonstrate their dedication to implementing robust security controls and protecting sensitive information from unauthorized access.
Obtaining SOC 2 compliance instills confidence in your existing customers and helps attract new ones. In today’s competitive market, potential clients often prioritize working with service providers who have proven their commitment to data security through independent audits like SOC 2.
How to Achieve SOC 2 Compliance: The Journey to Data Security Excellence
While achieving SOC 2 compliance may seem daunting at first glance, it can be broken down into several key steps.
1. Understand the Criteria
Familiarize yourself with the five trust service criteria outlined by AICPA – security, availability, processing integrity, confidentiality, and privacy. Each criterion has specific requirements that must be met to achieve compliance.
2. Identify Applicable Controls
Determine which controls are relevant to your organization based on its services and operations. The control objectives should align with the trust service criteria you identified earlier.
3. Implement Necessary Controls
Implement the required controls within your organization. This may involve measures such as access controls, data encryption, regular monitoring, and incident response protocols.
4. Conduct Regular Risk Assessments
Perform periodic risk assessments to identify potential vulnerabilities and evaluate the effectiveness of your implemented controls. This ensures that you stay proactive in addressing any emerging risks or changing security landscape.
5. Engage an Independent Auditor
Hire a qualified independent auditor who specializes in SOC 2 compliance audits. They will assess your organization’s controls and provide an opinion on whether you meet the necessary criteria for SOC 2 compliance.
The Benefits of SOC 2 Compliance: Looking Beyond Just the Regulatory Requirements
Achieving SOC 2 compliance offers several benefits beyond simply meeting regulatory requirements.
1. Enhanced Security Measures
Implementing the necessary controls for SOC 2 compliance strengthens your overall security posture. By doing so, you reduce the risk of data breaches and demonstrate your commitment to protecting customer information.
2. Competitive Edge
Being SOC 2 compliant can give you a competitive advantage over non-compliant competitors when attracting new clients or pursuing business partnerships. It serves as proof of your dedication to data security and privacy.
3. Customer Trust and Confidence
SOC 2 compliance reassures your customers that their sensitive information is handled with utmost care and protection. It fosters trust and confidence in your services, leading to stronger long-term relationships with clients.
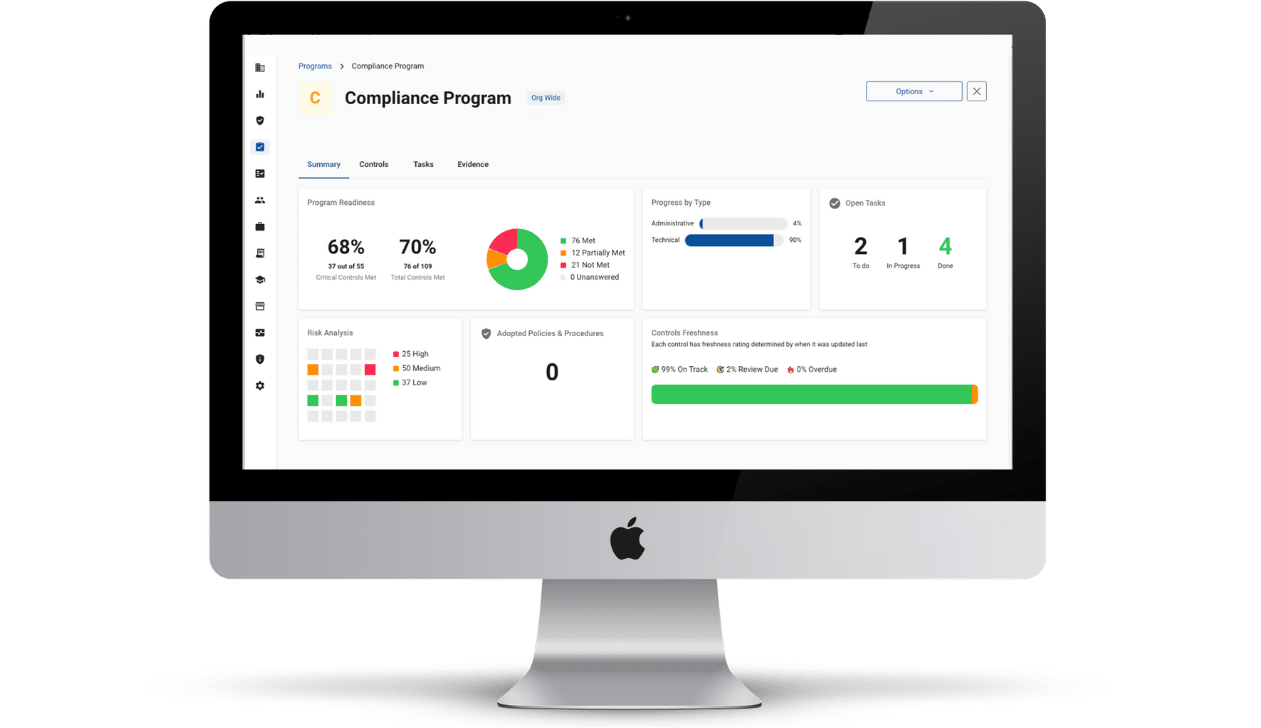
Achieving SOC 2 Readiness
SOC 2 compliance is a critical component of a robust data security strategy. By obtaining this report, organizations can demonstrate their commitment to safeguarding customer data and differentiate themselves in an increasingly competitive market. Through diligent planning, implementation of appropriate controls, regular audits, and continuous improvement efforts, businesses can achieve SOC 2 compliance while fostering trust among clients and stakeholders alike.
Do you need help with SOC 2 readiness? Compliancy Group helps you prepare and organize the documentation necessary for your SOC 2 audit. Streamline the risk assessment process and compliance reporting with comprehensive software.