The personal health information (PHI) of up to 15,000 patients who received medical care through Los Angeles County’s hospitals and clinics was exposed in a March, 2019 phishing scheme.
Nemadji Research Corp. is a business associate of the Los Angeles County Department of Health Services (DHS). The Department of Health Services oversees several clinics and hospitals in California, and is the second-largest health system in the nation. Nemadji assists DHS in verifying which patients are eligible for state health insurance programs, such as Medi-Cal, that could cover the cost of their care.
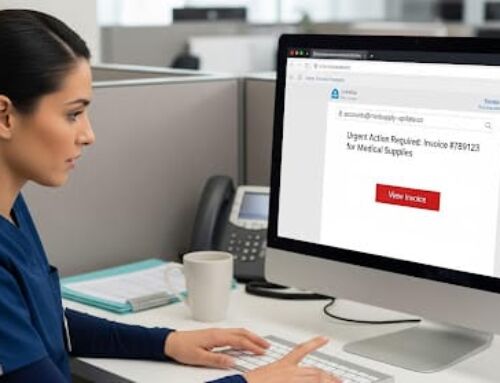
On March 28, 2019, a Nemadji employee fell victim to a phishing scheme. The employee opened the email, thereby allowing an unknown individual to access the employee’s email account for several hours.
While the data in the employee’s email account was encrypted, the account included decryption keys that made it possible for the unknown individual to access protected health information (PHI).
The data exposed by the phishing scheme includes patient names and addresses, dates of birth, medical records, and Medi-Cal identification numbers. Two patients’ Social Security numbers were also exposed.
Los Angeles County officials said that there was no evidence that its patients were the actual target of the phishing scheme, or that any patient information had been misused.
Nemadji, as required by California law, has offered access to free credit monitoring and identity protection services for anyone who may have been affected by the phishing scheme.
The company has also indicated that it has improved its email security systems and employee training since the attack.
How to Prevent Phishing Schemes
The Department of Health and Human Services’ (HHS) Office for Civil Rights (OCR) has released guidance on how to avoid falling victim to a phishing scheme. The guidance contains the following recommendations:
- Be wary of unsolicited third party messages seeking information. If you are suspicious of an unsolicited message, call the business or person that sent the message to verify that they sent it and that the request is legitimate.
- Be wary of messages even from recognized sources. Messages from co‐workers or a supervisor as well as messages from close relatives or friends could be sent from hacked accounts used to send phishing messages.
- Be cautious when responding to messages sent by third parties. Contact information listed in phishing messages such as email addresses, websites, and phone numbers could redirect you to the malicious party that sent the phishing message. When verifying the content of a message, use known good contact information or, for a business, the contact information provided on its website.
- Be wary of clicking on links or downloading attachments from unsolicited messages. Phishing messages could include links directing people to malicious websites or attachments that execute malicious software when opened.
- Be wary of even official looking messages and links. Phishing messages may direct you to fake websites mimicking real websites using website names that appear to be official, but which may contain intentional typos to trick individuals.
- Use multi‐factor authentication. Multi‐factor authentication reduces the possibility that someone can hack into your account using only your password.
- Keep anti‐malware software and system patches up to date.
- Back up your data.
Phishing schemes can be costly and negatively affect your organization’s reputation. Making sure your organization has proper safeguards in place to protect PHI can save your organization from phishing schemes and costly remediation efforts.
To address HIPAA cybersecurity requirements, Compliancy Group works with IT and MSP security partners from across the country. You can contract with these partners so that they can properly handle your HIPAA cybersecurity protection needs.
Find out more about how Compliancy Group helps you simplify compliance and cybersecurity today!