On December 14, 2021, the HHS Office for Civil Rights (OCR) issued a warning regarding a severe vulnerability in Java logging libraries that allows unauthenticated remote code execution and access to servers. The systems affected by the vulnerability use the Java logging library, Apache Log4j between versions 2.0 and 2.14.1, including applications and services written in Java. The RCE vulnerability is considered one of the more dangerous exploits ever discovered, affecting hundreds of millions of systems across every part of the internet.
Why You Should Be Concerned
The majority of SaaS applications use Apache Log4j, according to the Cybersecurity and Infrastructure Security Agency (CISA), “Log4j is very broadly used in a variety of consumer and enterprise services, websites, and applications—as well as in operational technology products—to log security and performance information. An unauthenticated remote actor could exploit this vulnerability to take control of an affected system.”
Since so many SaaS applications use Log4j, there is the potential that the vulnerability can lead to widespread healthcare cyberattacks. The Health Sector Cybersecurity Coordination Center (HC3) stated, “The exact extent to which Log4j is deployed throughout the health sector is unknown. It is a common application, utilized by many enterprises and cloud applications including several large and well-known vendors. Therefore, it’s highly likely that the health sector is impacted by this vulnerability, and possibly to a large-scale extent. Log4j is known to be a component in many software platforms, some of which are part of cloud services.”
The vulnerability affects JNDI features used in configuration, log messages, and parameters, failing to protect against attacker controlled LDAP and other JNDI related endpoints. Attackers who exploit the RCE vulnerability can control who can log messages or log message parameters, enabling them to execute arbitrary code loaded from LDAP servers when message lookup substitution is enabled. According to data from cybersecurity firm Check Point, there have been more than 100 hacking attempts reported per minute as a result of the flaw.
“It’s ubiquitous. Even if you’re a developer who doesn’t use Log4j directly, you might still be running the vulnerable code because one of the open source libraries you use depends on Log4j,” Chris Eng, chief research officer at cybersecurity firm Veracode, told CNN Business. “This is the nature of software: It turtles all the way down.”
How to Address the RCE Vulnerability
On December 13, 2021, Apache released Log4j version 2.16.0 in a security update to address what is known as the CVE-2021-45046 vulnerability. In version 2.16.0, the ability functionality that allows attackers to execute arbitrary code loaded from LDAP servers when message lookup substitution is enabled has been disabled.
CISA released guidance on how affected organizations can mitigate the vulnerability. They recommend the following:
- Review Apache's Log4j Security Vulnerabilities page for additional information and, if appropriate, apply the provided workaround:
- In releases >=2.10, this behavior can be mitigated by setting either the system property log4j2.formatMsgNoLookups or the environment variable LOG4J_FORMAT_MSG_NO_LOOKUPS to true.
- For releases from 2.7 through 2.14.1 all PatternLayout patterns can be modified to specify the message converter as %m instead of just %m.
- For releases from 2.0-beta9 to 2.7, the only mitigation is to remove the JndiLookup class from the classpath: zip -q -d log4j-core-*.jar org/apache/logging/log4j/core/lookup/JndiLookup.class.
- Apply available patches immediately. See CISA's GitHub repository for known affected products and patch information.
- Prioritize patching, starting with mission critical systems, internet-facing systems, and networked servers. Then prioritize patching other affected information technology and operational technology assets.
- Until patches are applied, set log4j2.formatMsgNoLookups to true by adding -Dlog4j2.formatMsgNoLookups=True to the Java Virtual Machine command for starting your application. Note: this may impact the behavior of a system's logging if it relies on Lookups for message formatting. Additionally, this mitigation will only work for versions 2.10 and above.
- As stated above, BOD 22-01 directs federal civilian agencies to mitigate CVE-2021-44228 by December 24, 2021, as part of the Known Exploited Vulnerabilities Catalog.
- Conduct a security review to determine if there is a security concern or compromise. The log files for any services using affected Log4j versions will contain user-controlled strings.
- Consider reporting compromises immediately to CISA and the FBI.
"It will take years to address this while attackers will be looking… on a daily basis [to exploit it]," said David Kennedy, CEO of cybersecurity firm TrustedSec. "This is a ticking time bomb for companies."
For more information from CISA on the RCE vulnerability, please click here.
Consult a Cybersecurity Expert
While the RCE vulnerability affects large businesses, it also exploits systems used by small organizations. These organizations, that most likely do not have dedicated IT staff, are often the most vulnerable to cyberattacks. "What I'm most concerned about is the school districts, the hospitals, the places where there's a single IT person who does security who doesn't have time or the security budget or tooling," said Katie Nickels, Director of Intelligence at cybersecurity firm Red Canary. "Those are the organizations I'm most worried about — small organizations with small security budgets."
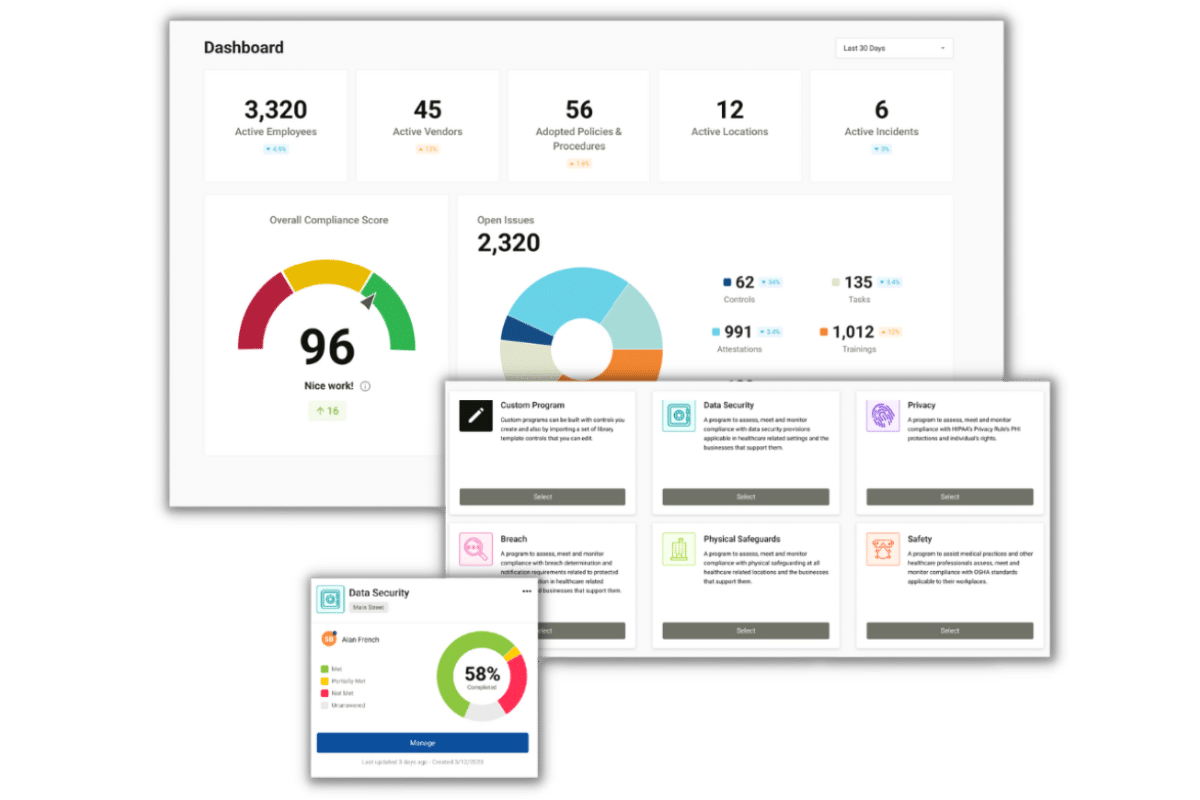
Compliancy Group can help connect you with a managed security service provider (MSSP) to help you address your cybersecurity concerns. Don't wait until you fall victim to a cyberattack. Find out how HIPAA compliance and advanced cybersecurity tools protect you against breaches and HIPAA fines.