As a Healthcare CISO You Need to Know About HIPAA Compliance
As your organization’s Chief Information Security Officer, you need to be aware of HIPAA’s security requirements. If your organization is working with protected health information, whether you’re a covered entity or business associate, you must comply with all of HIPAA standards. To ensure that your organization complies with HIPAA, healthcare CISO guidance is provided below.
What Are HIPAA Security Requirements?
As a healthcare CISO, your primary focus should be following HIPAA Security Rule guidance.
The HIPAA Security Rule requires that organizations:
- Ensure the confidentiality, integrity, and availability of all electronic protected health information (ePHI) they create, receive, maintain, or transmit;
- Identify and protect against reasonably anticipated threats to the security or integrity of the information;
- Protect against impermissible uses or disclosures of ePHI that are reasonably anticipated; and
- Ensure compliance by their workforce.
This is done by implementing administrative, technical, and physical safeguards. However, HIPAA does not necessarily tell you what those safeguards should be, just that they be “reasonably appropriate” for your organization.
The Security Rule does state that you should consider the following when determining what is “reasonably appropriate” for your organization:
- Size, complexity, and capabilities;
- Technical hardware, and software infrastructure;
- Costs of security measures; and
- The likelihood and possible impact of the potential risk to ePHI.
To determine what specific safeguards make sense for your organization to implement, you should conduct self-audits, including a security risk analysis. By conducting your self-audits, not only are you satisfying a HIPAA requirement, you identify the weaknesses and vulnerabilities in your current safeguards.
What Are HIPAA Safeguards?
HIPAA safeguards protect the confidentiality, integrity, and availability of protected health information. HIPAA requires you to implement what are referred to as administrative, physical, and technical safeguards.
Administrative Safeguards
To implement administrative safeguards you must first perform a risk analysis. Performing a risk analysis helps you to determine what security measures are reasonable and appropriate for your organization.
When conducting a security risk analysis you:
- Evaluate the likelihood and impact of potential risks to ePHI;
- Implement appropriate security measures to address the risks identified in the risk analysis;
- Document the chosen security measures and the rationale for adopting those measures; and
- Maintain continuous, reasonable, and appropriate security protections.
Administrative safeguards must include:
- Implementing security and risk management processes.
- Designating a security official, who will be responsible for the development and implementation of Security Rule policies and procedures. As a healthcare CISO, this will likely be you.
- Implementing workforce security measures such as designating and creating processes for PHI access levels, preventing unauthorized PHI access, and training employees.
- Implementing policies and procedures to address security incidents.
- Establishing policies and procedures for responding to an emergency or other occurrence that damages systems that contain ePHI.
- Performing a periodic technical and nontechnical evaluation that establishes the extent to which security policies and procedures meet the requirements of the Security Rule.
Physical Safeguards
Physical safeguards protect the physical security of your offices where PHI or ePHI may be stored or maintained.
Physical safeguards must include:
- Facility access and control measures to limit physical access to facilities, while allowing authorized access to ePHI.
- Workstation and device security including specifying proper use of and access to workstations and electronic media, in the form of written policies and procedures. Policies and procedures must also dictate processes for the transfer, removal, disposal, and re-use of electronic media.
Common examples of physical safeguards include:
- Alarm systems;
- Security systems; and
- Locking areas where PHI is stored.
Technical Safeguards
Technical safeguards include measures to restrict and track access to ePHI.
In addition to firewalls, encryption, and data backup, technical safeguards should include:
- Access controls to limit ePHI access to only authorized individuals.
- Audit controls to track who access what data, how long they access it for, and how frequently they access it.
- Integrity controls to ensure that ePHI has not been, and will not be, improperly altered or destroyed.
- Transmission security to prevent unauthorized access to ePHI that is transmitted over an electronic network.
How Can You Make Sure You’re Covered?
Even as a seasoned Chief Information Security Officer, it can be difficult to keep track of what your organization needs to have in place to be HIPAA compliant, especially as HIPAA rules and regulations change over time. This is why you should work with a HIPAA expert to ensure that you are doing everything that is required of you.
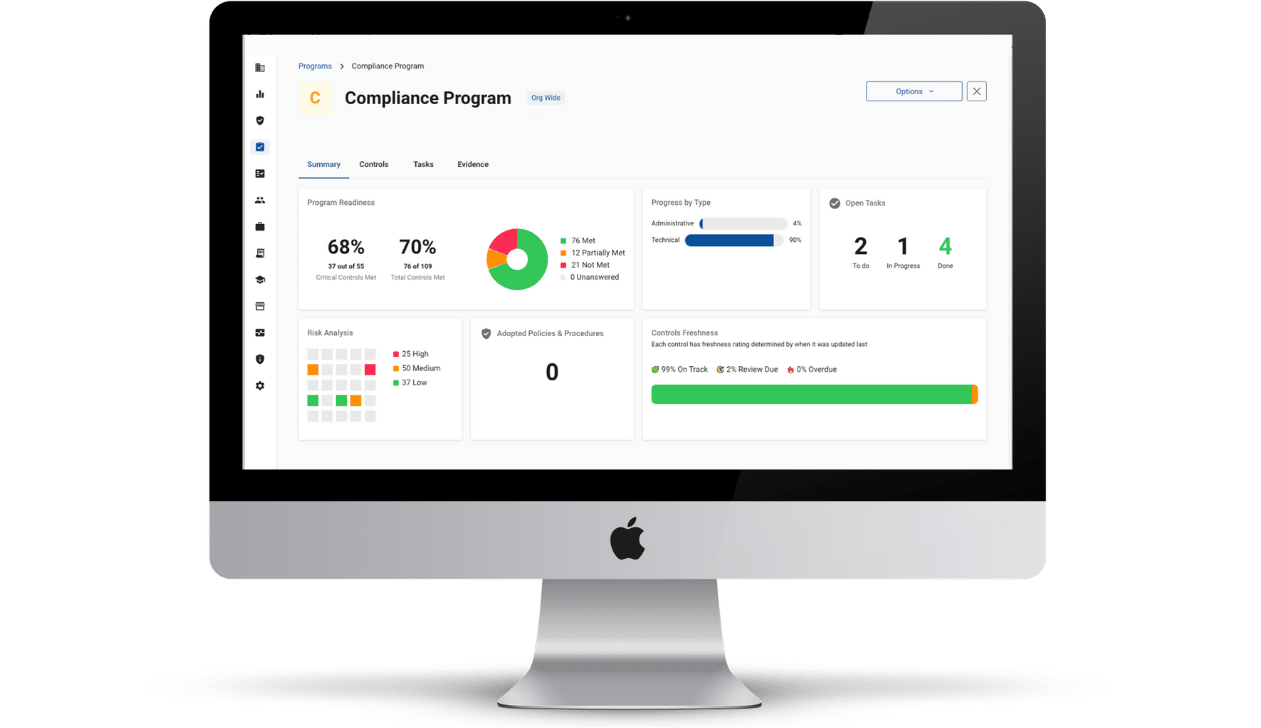
Compliancy Group gives you all the tools that you need to be a successful healthcare CISO. We assign you a dedicated Compliance Coach to walk you through every step of implementing an effective HIPAA compliance program.
This includes:
- Guided risk assessment, and other required HIPAA self-audits
- Gap identification and remediation
- HIPAA Security, Privacy, and Breach Notification policies and procedures
- Employee HIPAA, policy and procedure, and cybersecurity training
- Business associate agreements
- Incident response and audit support
Get the HIPAA guidance and support you need by speaking with us today!