Healthcare organizations often believe they are compliant—until enforcement action proves otherwise. The most common failure point is not a missing policy or incomplete training log. It is the absence of a defensible, well-documented, and continuously updated risk assessment.
To begin with, it’s important to understand that a risk assessment is more than just a checklist. It is a sign that you both understand risk in your business, and are acting accordingly. When conducted properly, risk assessment connects policies, training, technical safeguards, incident response, and vendor oversight into a unified system of accountability—but it only protects you if you can prove it.
This article outlines a practical, defensible framework for conducting healthcare compliance risk assessments that meet regulatory expectations and strengthen operational resilience.
Table of Contents
What Is a Healthcare Compliance Risk Assessment?
A healthcare compliance risk assessment is a structured process used to identify threats and vulnerabilities that could compromise data security, violate regulatory requirements, or expose an organization to enforcement, financial penalties, or reputational damage.
Risk analysis is not optional. In the event of an incident, regulators often begin investigations by requesting documentation of the organization’s most recent risk assessment. If that documentation is missing, outdated, or superficial, the organization’s compliance posture immediately weakens.
A defensible risk assessment answers four essential questions:
- What assets and workflows expose us to regulatory risk?
- What threats and vulnerabilities exist?
- How likely is exploitation, and what would the impact be?
- What safeguards are in place, and are they effective?
When these questions are addressed systematically—and documented—the organization moves from assumed compliance to demonstrable compliance.
Why Risk Assessments are the Lynchpin of Healthcare Compliance
Many organizations treat compliance as a series of disconnected activities: policies are written, employees are trained annually, vendors sign agreements, and audits occur periodically. However, without a centralized risk assessment tying these activities together, compliance efforts lack strategic direction.
A properly executed risk assessment becomes the connective tissue of the compliance program. It informs which policies need revision, where employee training must be strengthened, which technical safeguards require investment, and how incident response should evolve. It also drives prioritization. Not every vulnerability carries equal weight, and resource allocation should reflect risk severity rather than convenience.
Regulators consistently emphasize that enforcement often stems not from a single breach, but from a failure to assess and address known risks. In that sense, the risk assessment is less about predicting the future and more about demonstrating a “good faith effort” to identify and mitigate exposure before harm occurs.
Look at it this way: if you’re assessing risk, but not recording the specific steps you’ve taken to remediate your problem areas, you’ve just documented your failures in a way that could incriminate your business. A successful risk assessment needs to connect problems to solutions.
The Four-Step Risk Management Framework for Healthcare Organizations
An effective healthcare risk assessment follows a continuous cycle: identify, assess, address, and monitor. Each step builds upon the previous one, creating a defensible compliance infrastructure.
Identify: Discover Where Risk Lives
Risk identification should draw from multiple sources. Regulatory updates and enforcement trends provide insight into where oversight agencies are focusing attention.
Internal audits reveal control weaknesses before regulators do. Incident reports, including near-misses, highlight recurring operational gaps. Employee feedback often surfaces vulnerabilities that leadership may not see.
A mature identification process moves beyond assumptions and builds a documented inventory of assets, workflows, and threat vectors.
Assess: Evaluate Likelihood and Impact
Once risks are identified, they must be evaluated objectively. This is typically done using a structured scoring methodology aligned with established frameworks.
Risk scoring evaluates two primary dimensions: likelihood and impact. Likelihood considers the probability that a vulnerability will be exploited, taking into account threat actor capability, existing control effectiveness, and exposure surface. Impact evaluates potential harm, including patient safety implications, regulatory penalties, financial loss, operational disruption, and reputational damage.
By multiplying likelihood and impact, organizations can prioritize remediation efforts. High-risk findings require immediate attention, medium-risk findings require defined remediation timelines, and low-risk findings should be documented with an acceptance rationale.
The critical principle is this: not all risks are equal, and compliance resources should be directed where both likelihood and impact are high.
Address: Translate Findings into Action
A risk assessment that ends with a report is incomplete. The addressing phase converts analysis into measurable remediation.
This includes implementing or strengthening safeguards, updating policies and procedures to reflect operational reality, and delivering role-based employee training that targets identified vulnerabilities. Documentation is essential; regulators expect to see not only that risks were identified, but that remediation plans were assigned, tracked, and completed.
Each corrective action should have clear ownership, defined timelines, and written evidence of completion. Without documentation, remediation cannot be proven.
Importantly, policies must align with actual practice. If procedures describe safeguards that are not implemented in reality, the organization creates additional exposure. The addressing phase is as much about operational alignment as it is about regulatory compliance.
Monitor: Ensure Controls Remain Effective
Compliance is not static. Technology changes, staff turnover occurs, new ransomware variants emerge, and regulations evolve. Monitoring ensures that safeguards implemented today remain effective tomorrow.
Ongoing monitoring includes periodic internal audits, review of incident trends, testing of incident response processes, and tracking performance metrics such as remediation completion rates and training comprehension scores. It also requires organizations to reassess risk whenever significant changes occur, such as mergers, new service lines, cloud migrations, or adoption of artificial intelligence tools.
Monitoring feeds directly back into identification. This cyclical structure ensures the risk assessment remains a living process rather than a one-time annual exercise.
Applying the Framework to Healthcare Compliance
In practice, applying this framework begins with a comprehensive inventory of all assets and systems. Organizations must map where patient data is stored, transmitted, and accessed. Each system and workflow is then evaluated against administrative, physical, and technical safeguard requirements.
Threat scenarios—such as phishing attacks, insider misuse, lost devices, ransomware, or improper vendor access—are evaluated for likelihood and impact. Controls such as multi-factor authentication, access controls, encryption, employee training, and vendor agreements are analyzed for effectiveness.
Findings are scored, prioritized, and documented. High-risk findings typically require remediation within 30 days. Medium-risk findings are scheduled for remediation within defined timelines, often 90 days. Low-risk findings may be addressed during the next review cycle but must still be documented with justification.
Throughout this process, documentation becomes the organization’s strongest defense. A regulator may understand that no environment is risk-free. What regulators scrutinize is whether the organization knew about the risk and failed to act.
How Often Should a Risk Assessment Be Conducted?
In practice, annual comprehensive reviews represent the minimum acceptable cadence. However, risk assessments should also be revisited whenever significant organizational, regulatory, or technological changes occur.
Changes in ownership, new technology implementations, emerging cybersecurity threats, and evolving state privacy laws can all alter the organization’s risk posture. If the risk assessment does not reflect current operations, it cannot be considered accurate or defensible.
What Regulators Look for During an Audit
When regulators request a risk assessment, they are not only reviewing the final scorecard. They are evaluating methodology, leadership involvement, documentation discipline, and alignment between identified risks and corrective actions.
They expect to see a clear inventory of assets, a documented scoring rationale, evidence of mitigation planning, and proof that leadership was informed. They also look for evidence that risk findings informed employee training, policy updates, and monitoring activities.
The absence of documentation often signals a broader compliance gap. Conversely, thorough documentation demonstrates organizational diligence—even when vulnerabilities exist.
Frequently Asked Questions
What is the purpose of a risk assessment?
The purpose is to identify and evaluate risks to electronic protected health information and to implement safeguards that reduce the likelihood and impact of regulatory violations or data breaches.
Is a risk assessment required every year?
Most regulators have moved away from “annual” terminology to “ongoing”. Your risk assessment should be a living document, that is regularly updated as needed, with a regular review cadence associated with it. In-depth assessment can be completed when significant operational changes or technological changes occur.
What happens if an organization does not conduct a risk assessment?
Failure to conduct and document a risk assessment significantly increases exposure during enforcement actions. Regulators often request this documentation first, and its absence can form the basis for penalties.
Who should participate in the risk assessment process?
Compliance, IT, operations, leadership, and relevant department heads should collaborate to ensure the assessment reflects actual workflows and control effectiveness.
From Required to Ready: Building Compliance Maturity
Organizations often begin their compliance journey focused on baseline requirements. Mature organizations move beyond minimal compliance toward operational resilience. In this model, risk assessment is not merely a regulatory requirement; it becomes a strategic tool that drives governance, accountability, and continuous improvement.
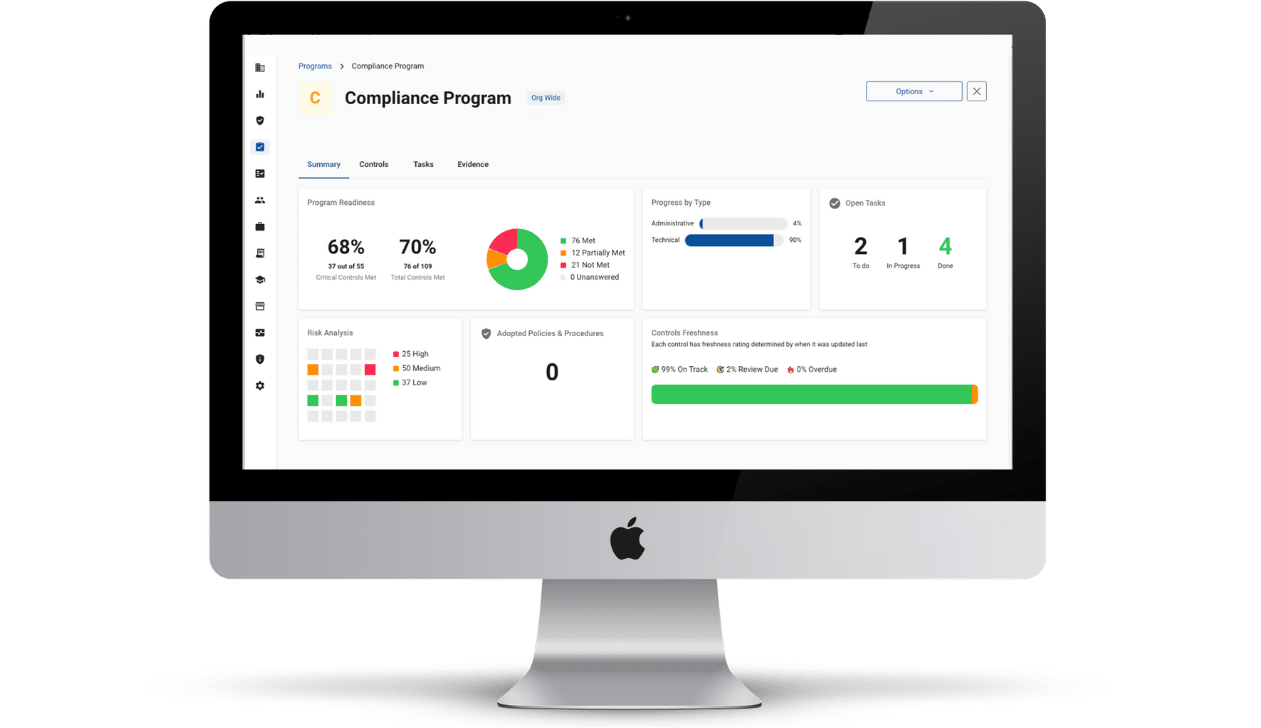
Managing healthcare compliance starts with a clear, documented view of organizational risk. Many organizations turn to The Guard for this stage in their compliance journey, as it offers a single, central location for all compliance activity. Risk management gets its own dedicated area, but every aspect of your business’s compliance strategy is visible, connected, and provable.
Healthcare compliance is not about eliminating all risk. It is about identifying risk, prioritizing intelligently, documenting decisions, and demonstrating ongoing vigilance. The Guard ensures that your organization is always audit-ready, making your compliance activities demonstrable and thereby keeping your business shielded and secure. Learn more about how The Guard can help your healthcare organization guide, track, prove, and reduce organizational risk.