As 2022 unfolds, the security and compliance threats to organizations and healthcare practices look a lot like a repeat of 2021: more ransomware threats, recycling old scams and finding new flaws to exploit.
Where should your focus be regarding 2022 security and compliance, and what are the best 2022 healthcare security tips to protect your organization?
2022 Security and Compliance Tips, Threats, and Trends – Ransomware on Repeat, Questionable QRs
If Ben Franklin were alive today, he’d likely amend his famous adage to, “…nothing is certain except death and taxes and ransomware.” From January 1 to February 18, 2022, the U.S. Department of Health and Human Services Office for Civil Rights Breach Portal (aka, the Wall of Shame) received reports of 52 hacking incidents. That is nearly double the 27 incidents reported during the same period in 2021.
In fact, ransomware is expected to surpass phishing attacks as the leading cause of all data breaches in 2022, according to an Identity Theft Resource Center report.
While the Coinbase floating QR code ad during the Super Bowl worked as hoped (except perhaps the part where web traffic crashed their servers) it also highlights the potential threat of malicious QR codes raised by the FBI in January.
Bad actors are leveraging the pandemic-fueled resurgence in the use of QR codes to redirect unsuspecting users to malicious websites in ways that can bypass conventional email security procedures.
In a video produced before Coinbase’s ad aired, Pax8’s Senior Director of Security and Compliance Matt Lee demonstrated how a legitimate restaurant QR code could be created and replaced in less than three minutes.
2022 Security and Compliance Tips, Threats, and Trends – Build from the Inside
As external cybersecurity threats grow, your workforce can be your greatest vulnerability or a vital part of your security. It all depends upon what kind of security culture you create within your organization.
Another 2022 healthcare security tip is regular education and training to raise awareness of the potential threats and how harmless they first appear. This could include mock phishing and ransomware attacks on your systems.
Because of the regulations and rules regarding privacy and security, HIPAA compliance can be the cornerstone of building a culture that incorporates security awareness as part of everyday operations.
2022 Security and Compliance Tips, Threats, and Trends – Zero (Trust) is a Hero
Another foundational principle for your culture of compliance and security is Zero Trust. The term is used widely in information security circles, but what is it, and how can it protect your business?
Simply put, Zero Trust requires that you operate with a mindset that every request for data or access to your network or systems is a threat. That doesn’t mean you have to build aluminum foil hats for your servers. It means that you must configure your security controls to identify legitimate users from those who would harm your clients and organization.
Zero Trust incorporates digital authentication and behavioral analysis tools to limit access to authorized users. Like HIPAA compliance, you can’t just buy it off the shelf and attach it to your system. Zero Trust must be a mindset within your organization’s security culture to be truly effective.
Cybercriminals are constantly discovering new vulnerabilities and creating new threats to exploit them. Security is a journey, not a destination.
2022 Security and Compliance Tips, Threats, and Trends – MFA is A-OK
Digital identities and access control are two key things businesses can control to maintain security. Verification of those credentials has gone far beyond the days of a simple password. Threat actors can utilize social engineering attacks (phishing) or brute force attacks (guessing passwords).
Two- or Multi-factor Authentication (MFA or 2FA) adds additional verification options in addition to or even in place of passwords. One-time use codes sent via text to a user’s phone or a code generated by a USB security token are examples of factors that incorporate something that is possessed. Another form of authentication utilizes biometric information specific to each user, like retina scans or fingerprints, to further enhance security.
2022 Security and Compliance Tips, Threats, and Trends – You Need Cyber Insurance, but Can You Get it?
Many experts advise that companies seriously consider adding dedicated cyberattack or cybersecurity insurance to their arsenal to defend against ransomware and hacking attacks. Following this healthcare security tip may not be as easy as in past years.
Substantive changes are happening in the insurance marketplace, as states and underwriters recognize the financial exposure and increasing possibilities of these incidents and the high price of covering the potential losses.
The state of New York has issued a framework of guidelines for insurance companies which includes requiring law enforcement notification, managing and eliminating exposure in policies that do not specify cyber coverage, evaluating systemic risks such as liability for damages to the insured’s customers, and rigorously measuring potential risk to those they insure.
Those rigorous measurements are likely to include minimum basic security protocols like MFA and Zero Trust and evaluations of an insured organization’s culture to secure and maintain data privacy. Part of that will almost certainly include compliance with any legal requirements such as HIPAA.
A healthcare practice or business associate may be turned down for cyber insurance or may even have a claim denied if they are not compliant with HIPAA rules and regulations. A ransomware incident will likely lead to a breach resulting in violations and substantial fines.
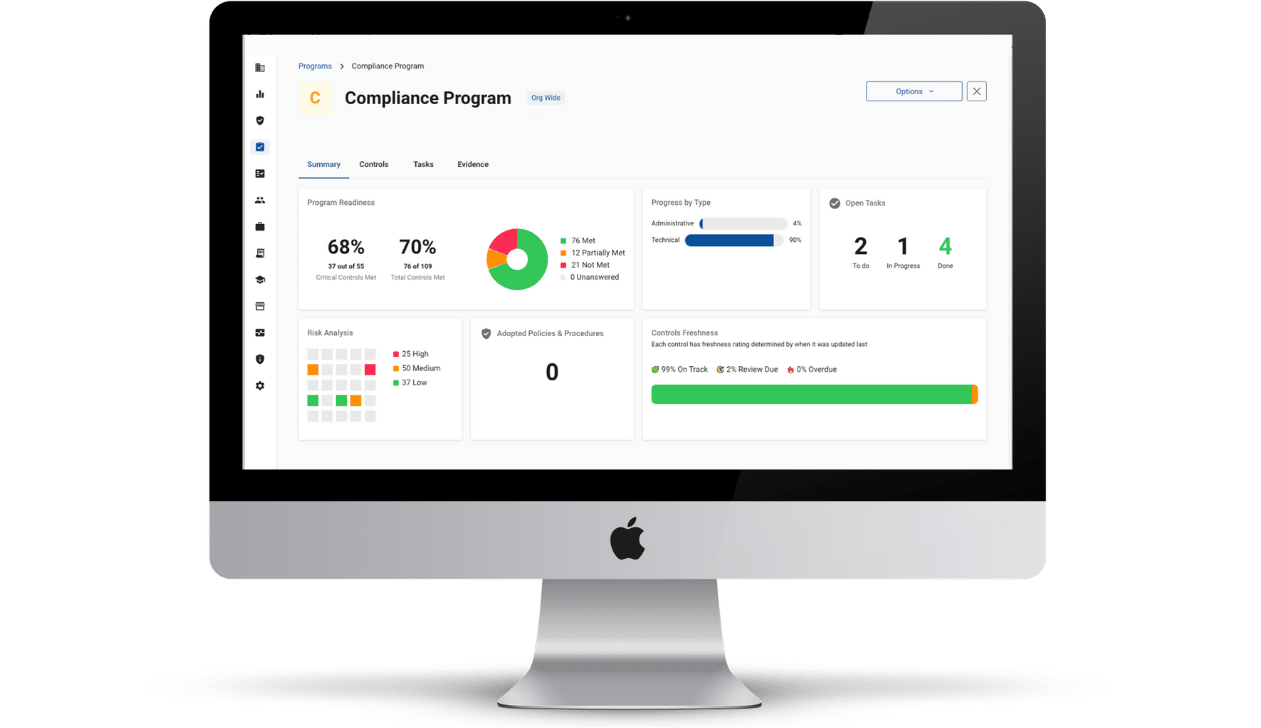
Compliancy Group has nearly 20 years of successfully guiding companies through the confusing process of becoming fully HIPAA compliant in a way that minimizes stress and maximizes support. We also have a network of endorsed HIPAA compliant partners with the knowledge and expertise to direct your data security and privacy efforts in the way that works best for you.
Interested in becoming a partner? Find out more about Compliancy Group’s Partner Program.