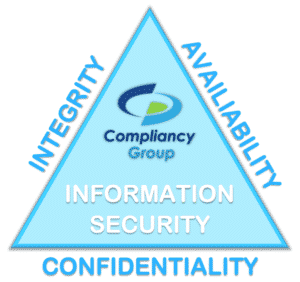
 Confidentiality, integrity, and availability are essential components of any effective information security program. Sometimes referred to as the ‘CIA triad,’ confidentiality, integrity, and availability are guiding principles for healthcare organizations to tailor their compliance with the HIPAA Security Rule.
Confidentiality, integrity, and availability are essential components of any effective information security program. Sometimes referred to as the ‘CIA triad,’ confidentiality, integrity, and availability are guiding principles for healthcare organizations to tailor their compliance with the HIPAA Security Rule.
HIPAA regulation sets specific guidelines for maintaining the privacy and security of protected health information (PHI). These guidelines are organized into a collection of HIPAA Rules. The HIPAA Security Rule sets national standards that HIPAA-beholden entities must implement in their organizations. PHI is any demographic information that can be used to identify a patient. Common examples of PHI include names, addresses, telephone numbers, Social Security numbers, email addresses, financial information, insurance ID numbers, and medical records, to name a few. When PHI is stored in electronic form, it’s known as electronic protected health information (ePHI).
Part of the HIPAA Security Rule outlines administrative, technical, and physical security measures that HIPAA-beholden entities must have in place. The purpose of these safeguards is stated in the regulation as being used to ensure the confidentiality, integrity, and availability of PHI.
For that reason, the confidentiality, integrity, and availability of PHI (the CIA triad) are direct offshoots of how well an organization addresses the HIPAA Security Rule. The Rule entails:
- Administrative: These are safeguards that have to do with internal policies and procedures and proper employee training. Documented security policies and procedures create a uniform process that staff members can follow to maintain the security of PHI. By implementing administrative safeguards, you can mitigate the potential for a security breach relating to human error.
- Technical: These are safeguards that include network and data security. Technical safeguards include measures your business can take to reduce the risk of a cyber-security incident, especially relating to improper transmission of ePHI over email or malware.
- Physical: These are safeguards that protect the physical premises of your business in regards to PHI and infrastructure that can access ePHI. Physical safeguards for the CIA Triad include locks and security systems to protect your office from PHI breaches associated with break-ins.
Confidentiality, integrity, and availability have a direct relationship with HIPAA compliance. One of the best ways to address confidentiality, integrity, and availability is through implementing an effective HIPAA compliance program in your business.
Confidentiality
Confidentiality is about ensuring the privacy of PHI. In order to maintain the confidentiality of PHI according to the CIA triad, organizations must have the physical, technical, and administrative safeguards in place, as outlined above and in HIPAA regulation. These safeguards ensure that PHI is not made available or disclosed to unauthorized individuals. Confidentiality is a function of compliance with HIPAA administrative safeguards.
Individuals who are legally allowed to access PHI should be trained about potential security risks that could threaten the confidentiality of PHI. This includes cybersecurity awareness training, outlined in HIPAA. Developing an effective HIPAA compliance program will overlap with confidentiality best practices to give your business the tools it needs to manage and safeguard access to PHI.
Integrity
According to the CIA triad, integrity has to do with how PHI is handled to ensure that it is not altered or destroyed in an unauthorized manner. Healthcare professionals looking to address the integrity of PHI must ensure that it is not changed, altered, or modified over the course of its lifecycle, especially when in transit. In the CIA triad, Integrity is a function of adhering to HIPAA administrative and technical safeguards.
Data should be closely monitored with systems in place to detect any improper or unauthorized changes to PHI. Maintaining the integrity of PHI will give your patients and clients a higher quality of care and protect you from potential HIPAA violations.
Availability
Availability is about keeping systems and hardware that store and access PHI functioning properly. This includes keeping all systems up-to-date and protected against threats such as ransomware, which can threaten access to PHI. Availability is a function of HIPAA technical and physical safeguards.
Keeping data backed-up and encrypted can act as failsafes to maintain availability in the event that a large scale cybersecurity incident does occur. Data backup will ensure that PHI can be restored in the aftermath of an incident or human error. Encryption can protect transmissions of PHI and defend against malware or ransomware incidents, which are increasingly targeting healthcare companies for valuable medical data.
Bringing it Together
The understanding that confidentiality, integrity, availability, and all that come with this package can grant your organization additional protections to PHI and work toward your compliance with HIPAA can make you more secure.
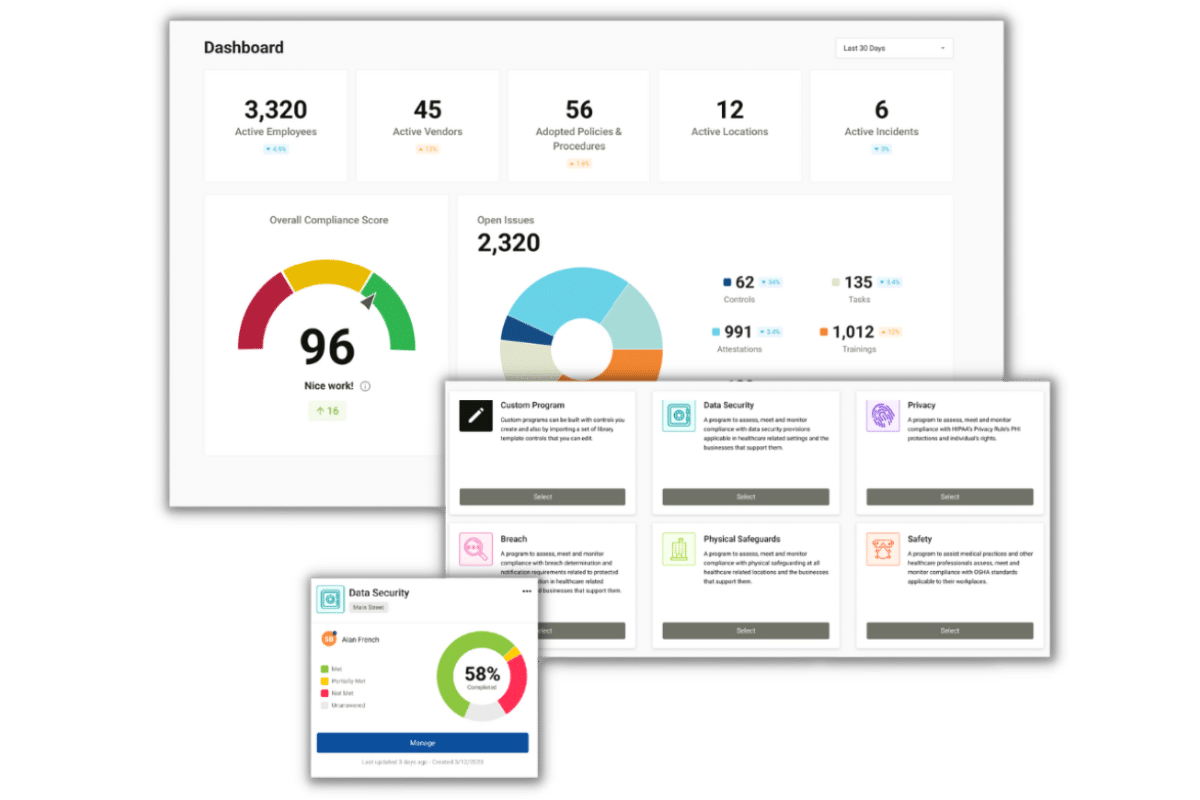
However, security is not enough to satisfy the law, nor is it enough to protect your organization from data breaches and fines. HIPAA compliance is a complex, interlocking set of national standards that must be addressed through the implementation of an effective compliance program. A good compliance program, uniformly applied across your entire business can ensure the confidentiality, integrity, and availability of PHI.
To find more resources about how to develop and implement an effective compliance program in your practice, check out our HIPAA Basics Guide.
If you’re ready to develop a HIPAA compliance program yourself, get on board with the trusted HIPAA advisors at Compliancy Group. Compliancy Group gives healthcare professionals the tools to become confident in their compliance, so they can focus on running their business. With Compliancy Group, you get ongoing, guided support from our team of expert Compliance Coaches.