What Are HIPAA Software Requirements?
Healthcare organizations generally use a variety of software tools to help them efficiently run their businesses. While there are many options for organizations to choose from when selecting which software services are right for their business, healthcare businesses must consider HIPAA. This is because when a healthcare business uses a software service to create, store, transmit, or receive protected health information (PHI), they must ensure that the service they use is HIPAA compliant. So how can you make sure that your software is HIPAA compliant so that you can work with healthcare clients? HIPAA software requirements dictate minimum standards that must be met to be considered HIPAA compliant.
HIPAA Software Security Requirements
Whether you are developing software, an app, or both, the security requirements are the same. These security requirements, referred to as safeguards, must ensure the confidentiality, integrity, and availability of electronic protected health information (ePHI).
End-to-End Encryption
Software developers must ensure that all ePHI is encrypted, included when it’s being sent, received, or stored. Encryption must follow SSL and HTTPS protocols to protect pages, including login pages, that collect or display ePHI.
While many developers think about the security of their software itself, cloud storage security is often overlooked. According to a recent study conducted by McAfee, 2020 saw a 630% increase in cyberattacks targeting cloud service providers. If you are using a public cloud or a private cloud to store ePHI, it must allow configuration of your SSL to prevent unauthorized cloud data access.
Data Backup
HIPAA requires exact copies of ePHI to be stored in an offsite data storage facility. This is to ensure that ePHI is always available in situations where a natural disaster, accident, or hacking incident compromises ePHI stored onsite.
User Authentication, Access Management, and Audit Logs
As part of HIPAA software requirements, ePHI access must be limited to the minimum necessary to perform a job function. Under the minimum necessary standard, only employees that require access to ePHI should be granted access. As such, software platforms must enable each of an organization’s employees to be given unique login credentials to access the platform. Through unique login credentials, administrators can implement access controls to designate different access levels for each employee dependent on their job function. These unique login credentials also enable ePHI access to be tracked and recorded through audit logs. By keeping audit logs impermissible access to ePHI can be detected quickly.
Automatic Logoff
To prevent unauthorized access to ePHI, it is important that software platforms enable automatic logoff procedures after a period of inactivity. Administrators should be able to choose appropriate automatic logoff times. For instance, software that is accessed from a front desk computer of a doctor’s office would need to have a shorter automatic logoff time than on a computer in a room protected by locks.
HIPAA Software Requirements and Administrative Considerations
As a software provider with healthcare clients, you are considered a business associate. As a business associate, in addition to building security controls into your software, there are administrative considerations to take into account.
Signing Business Associate Agreements
One of the most important factors that define a HIPAA compliant software provider is the willingness to sign a business associate agreement (BAA). Even the most secure software platform cannot be considered HIPAA compliant if they don’t sign BAAs with their healthcare clients.
A BAA is a legal agreement between a healthcare organization and their business associate that requires each signing party to be HIPAA compliant and to be responsible for maintaining their compliance. A BAA offers protection for both parties in the event of a breach if one of the parties is found noncompliant. This is because only the negligent party would be found liable, and be subject to HIPAA fines and corrective actions.
You Yourself Need to Be HIPAA Compliant
Now that you have built your software with HIPAA in mind, implementing all of HIPAA software security requirements, you need to implement an effective HIPAA compliance program. As a business associate, you are required to meet the standards set forth by HIPAA.
To be a HIPAA compliant business associate, you must:
- Conduct Annual Self-Audits: to assess your administrative, physical, and technical safeguards you must conduct annual self-audits. Self-audits measure your current safeguards against HIPAA standards to uncover gaps in your security practices.
- Address Risks and Vulnerabilities: by conducting annual self-audits, risks and vulnerabilities to your ePHI are uncovered. To be HIPAA compliant, you must address these risks and vulnerabilities with remediation plans. Remediation plans must be specific, including how deficiencies will be corrected, who is responsible for correcting them, and a timeline in which they will be addressed.
- Have Documented HIPAA Policies and Procedures: each organization is required to have written policies and procedures that directly apply to how their business operates. These policies must dictate the proper use and disclosure of ePHI, how your organization protects ePHI, and what to do in the event of a ePHI breach.
- Conduct Annual Employee Training: HIPAA requires any employee that has the potential to access ePHI to receive annual training. Training should include HIPAA basics, an overview of your organization’s policies and procedures, and cybersecurity best practices. Employee training must be tracked to ensure that employees are trained in a timely manner. Employees must also legally attest that they have read and understood the training material, and that they agree to adhere to it.
- Incident Detection and Response: it is important to have a system in place for preventing, detecting, and responding to breaches. Quick detection and response to breaches drastically limits the scope of the breach, the costs associated with it, and the amount of time it takes to recover from the incident.
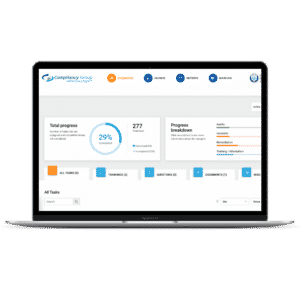
While all of this may seem overwhelming, there is an easy way to meet HIPAA software requirements. By working with Compliancy Group, you can become HIPAA compliant quickly and easily. Our streamlined process allows you to achieve HIPAA compliance with ease. What’s even better is that our HIPAA software dashboard provides you with a single-pane overview of your compliance program. From the dashboard, you can track your progress, see your open tasks, and complete your training.