Ransomware attacks are the most common type of malware incident in the healthcare industry, with 85% of all malware incidents classified as ransomware. A ransomware attack occurs when a hacker gains access to an organization’s network rendering data unusable until a sum of money is paid. In many cases, hackers maliciously encrypt the organization’s files so that patient files cannot be accessed. For covered entities, the inability to access patients’ files can have serious implications, such as preventing post operative care. In a recent ransomware attack, an ENT had to close their office after a ransomware attack left them without patient files. Not only could they not access patients’ files, they also lost access to their business calendar. With the inability to look up patient appointment times, one of the doctors had to wait around in the office to see if any patients showed up.
With so many healthcare organizations being targeted, it is important to know what to do if you’re a victim of a ransomware attack and how to prevent one from occurring.
What to do
- Remove infected device from network immediately: disconnecting affected devices from your internal network ensures that other devices connected to the network cannot be infected.
- Shut down affected devices: if the device has not been completely corrupted, it is essential to power down the device. This way it is possible to recover uncorrupted data.
- Restore data: once the device is disconnected from the network, you can restore files that have not been corrupted by malware.
- Change passwords: after the infected device is removed from the network, all system passwords must be changed. Failing to change passwords can leave the targeted organization vulnerable to further attacks.
How to Prevent Ransomware Attacks
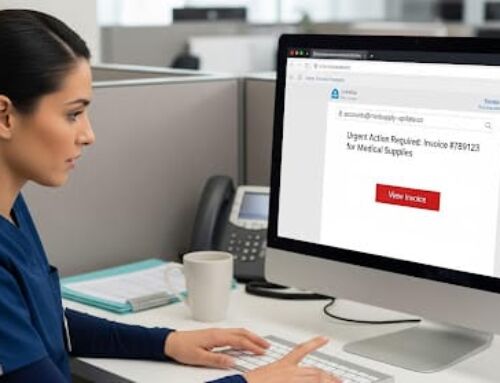
- Train employees: employees should not be using their work computers for personal reasons or opening email links from unfamiliar sources. Additionally, employees should learn how to identify and report phishing emails.
- Secure systems: organizations should encrypt data, install firewalls, endpoint protection and antivirus, and update systems periodically.
- Monitor network: file access and network traffic should be monitored to ensure that unauthorized users are not accessing sensitive data.
- Backup data: allows systems to be restored in the event of a breach. Without data backup, an organization is at risk for a ransomware attack. Organizations that choose not to pay may lose all of their data.
- Additional protection: IT staff should install safeguards to filter out suspicious sites and block harmful emails.
Do You Need Help with Cybersecurity?
Compliancy Group gives healthcare providers and vendors working in healthcare the tools to confidently address their HIPAA compliance in a simplified manner. Our cloud-based HIPAA compliance software, the Guard™, gives healthcare professionals everything they need to demonstrate their “good faith effort” towards HIPAA compliance.
To address HIPAA cybersecurity requirements, Compliancy Group works with IT and MSP security partners from across the country, who can be contracted to handle your HIPAA cybersecurity protection.
Find out more about how Compliancy Group helps you simplify compliance and cybersecurity today!