American Medical Technologies recently discovered an email breach that affected 47,767 patients. Details about the American Medical Technologies email breach are discussed below.
Is your organization secure?
Find out now with our HIPAA compliance checklist.
American Medical Technologies Email Breach: What Happened
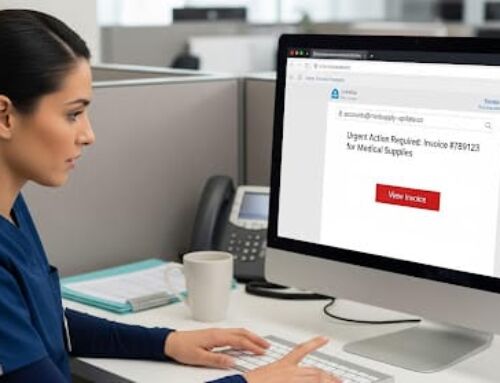
On December 17, 2019, American Medical Technologies (AMT) discovered that one of their employee’s email accounts had been hacked. Upon discovery, AMT contracted a third-party forensics firm to investigate the email breach. After a five month investigation, it was uncovered that patients’ protected health information (PHI) may have been compromised.
The 47,767 patients affected by the American Medical Technologies Email Breach will receive free credit monitoring services. In addition, since discovering the email breach, AMT has made improvements to bolster the security of its email systems and web server infrastructure.
American Medical Technologies Email Breach: How to Prevent an Email Breach
There are several ways in which the American Medical Technologies email breach could have been avoided.
◈ Policies and Procedures. To ensure adherence to HIPAA standards, it is essential to have policies and procedures in place. Policies and procedures determine the safeguards that organizations are required to have in place, allowing the confidentiality, integrity, and availability of PHI to be maintained.
◈ Email Encryption. Encryption prevents unauthorized access to PHI by masking the sensitive data. Encrypted data can only be accessed with a decryption key. However, email encryption cannot mask subject lines or the name of an email attachment. As such, PHI should never be contained in an email subject line or in the name of an email attachment.
◈ Multi-factor Authentication. Through multi-factor authentication (MFA), sensitive data is further secured. MFA utilizes multiple login credentials, such as a username and password in combination with another unique identifier (i.e., security questions, one-time PIN, biometrics, etc.), to authenticate users. Utilizing MFA reduces the risk of unauthorized access to PHI. For instance, if an employee’s username and password is compromised, hackers would be unable to access data without access to the employee’s other credentials.
◈ Employee Training. A key component to preventing email breaches is employee training. Employees that are trained to recognize a phishing email are less likely to click on malicious links.