The Health Insurance Portability and Accountability Act (HIPAA) established a set of standards that anyone working in healthcare must adhere to. HIPAA law is meant to safeguard a patient’s protected health information (PHI) to ensure that only those who need access to PHI, as part of their job, have access. Since HIPAA security law is complicated, many practices opt to hire IT solution providers to address their technology security, these IT providers are considered business associates (BAs).
What many medical providers fail to realize is that the business associates they are working with must also be HIPAA compliant. When a covered entity (CE) does not properly vet their vendors, they are liable for any breach that their business associate may experience. This is why it is imperative to do your technical due diligence and have a business associate agreement (BAA) in place before conducting business with a vendor.
What is a Business Associate Agreement?
A business associate agreement (BAA) is a legally binding contract that must be signed by all of your vendors that touch PHI, before any PHI can be transmitted. The BAA determines how the business associate may use PHI and can also include what they need to do to protect PHI, such as data encryption and device access controls.
In addition, a BAA mitigates liability in the event of a data breach. Without a BAA, when a breach occurs, both parties will be held accountable. A BAA, in most cases, ensures that only the party responsible for the breach is sanctioned. A business associate agreement can also provide guidelines for how to handle a data breach, for instance, who is responsible for reporting the breach. However, a business associate agreement is not enough when proving HIPAA compliance.
How to Vet your Business Associates
Vetting your business associates is required by HIPAA law; it is a covered entity’s responsibility to verify that the PHI they are transmitting is protected. As such, a HIPAA risk assessment should be completed by all of your vendors. A HIPAA risk assessment is a set of questions that determines whether or not the proper safeguards are in place to protect PHI. HIPAA standards mandate that there must be administrative, technical, and physical safeguards in place.
- Administrative safeguards are written policies and procedures that establish how PHI can be accessed and used.
- Technical safeguards are security measures such as data encryption and firewalls.
- Physical safeguards are related to your location’s security, i.e. an alarm system and locks on the doors.
Completing a HIPAA risk assessment identifies any gaps that may inhibit a BAs ability to safeguard protected health information. After the risk assessment is completed, any gaps identified must be addressed before a CE can conduct business with that vendor. If the vendor refuses to complete a risk assessment, or they complete a risk assessment but are unwilling to implement the changes necessary to be HIPAA compliant, the covered entity should end their business relationship with that vendor.
Need Help Managing your Business Associates?
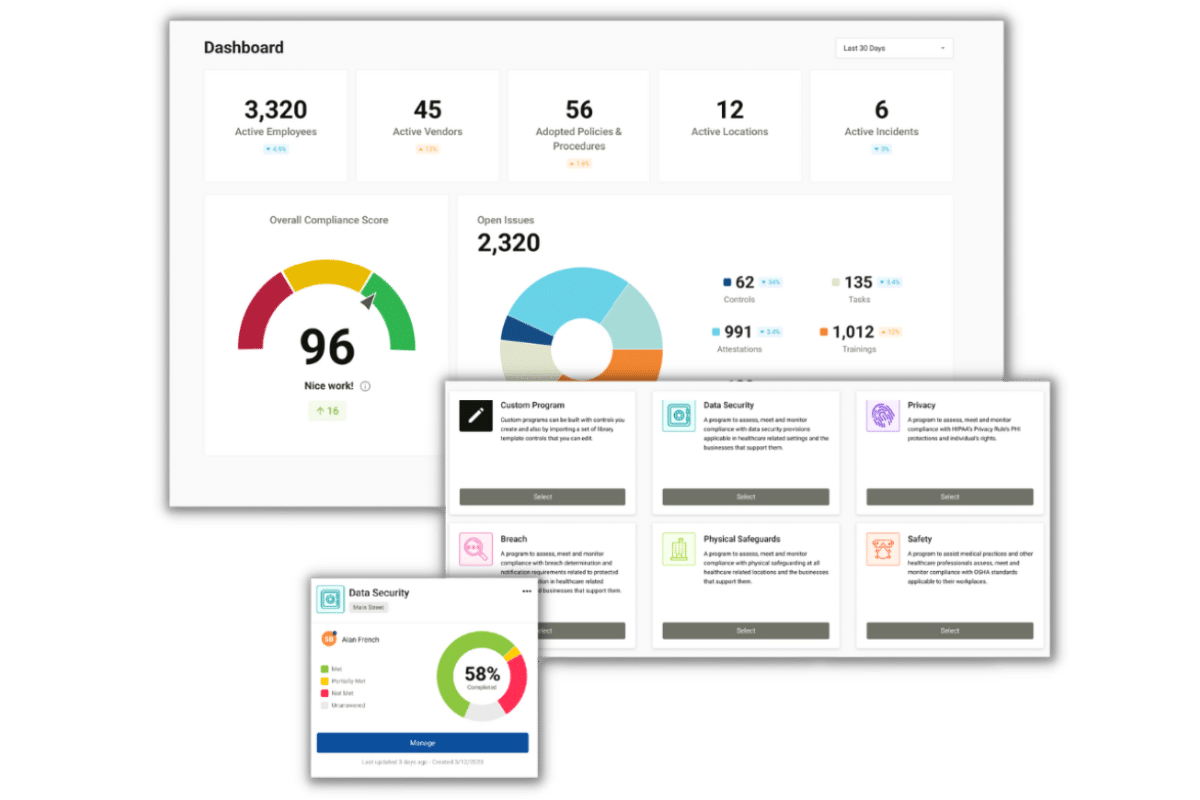
Compliancy Group simplifies HIPAA compliance so you can confidently focus on your business. Our cloud-based software platform, the Guard™, has the tools you need to manage your business associate relationships. We offer business associate agreements, that have been tested against the letter of the law, as well as HIPAA risk assessments. Learn more about how Compliancy Group can help!