A cybersecurity flaw responsible for widespread disruptions of applications and web services has the potential to adversely affect medical device security around the world.
How the Log4j Hacks Threaten Medical Device Security
Hackers found a vulnerability in the open-source Apache logging library Log4j that gives them the ability to take control of a machine very quickly and easily. The Log4Shell hack requires a minimal level of coding knowledge, increasing the number of potential hackers who may be trying to exploit the vulnerability.
Microsoft reports that threat actors have used the vulnerability to install cryptominers on vulnerable systems, steal system credentials, burrow deeper within compromised networks, and steal data. More than three billion devices worldwide use the log4j code to monitor security and performance data, including medical devices and supporting systems.
If these breaches result in a violation of HIPAA regulations, it could result in significant fines.
Mitigating the Danger of Log4j Threats to Medical Device Security
During a call with leaders from local governments, banking, and hospitals, Cybersecurity and Infrastructure Security Agency (CISA) Director Jen Easterly said the flaw, “is one of the most serious I’ve seen in my entire career, if not the most serious.”
The Food and Drug Administration has urged medical device manufacturers to “assess whether they are affected by the vulnerability, evaluate the risk, and develop remediation actions.”
“As Apache Log4j is broadly used across software, applications, and services, medical device manufacturers should also evaluate whether third-party software components or services used in or with their medical device may use the affected software and follow the above process to assess the device impact.”
CISA recommends asset owners take three additional, immediate steps regarding this vulnerability:
- Enumerate any external-facing devices that have log4j installed.
- Make sure that your security operations center is actioning every single alert on the devices that fall into the category above.
- Install a web application firewall (WAF) with rules that automatically update so that your Security Operations Center is able to concentrate on fewer alerts.
Maintain HIPAA Compliance to Improve Medical Device Security
As security incidents like the Log4Shell hack become more common, medical practices and the vendors who serve them must stay up to date on these potential threats. A breach can expose protected health information or deny access to important files and systems that could adversely affect patient care.
Having qualified support team members to manage your computer security is only part of the solution. Nearly 80 percent of all breaches occur because of administrative failures. Most often they occur because of ineffective policies and procedures, gaps in training, or failures to properly document attestations and training.
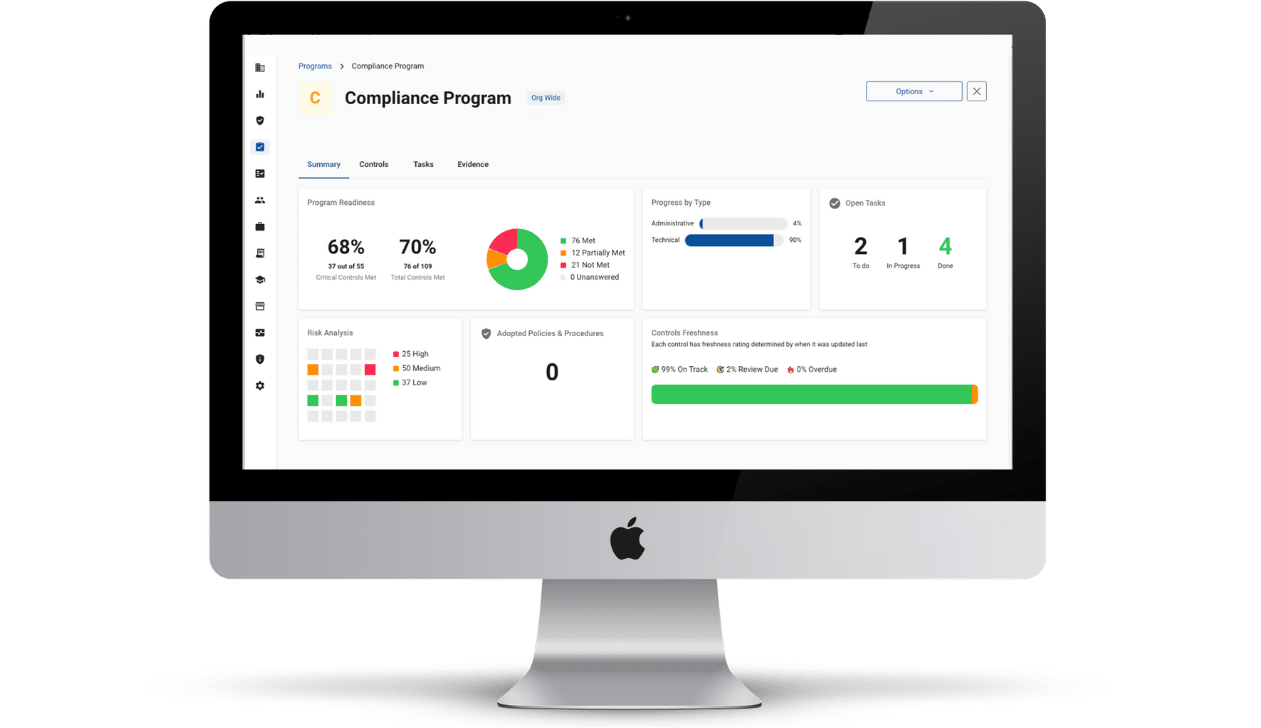
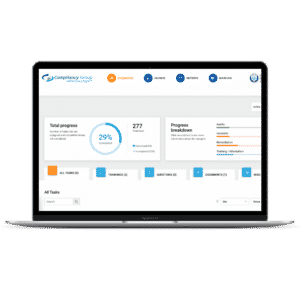
Compliancy Group offers a centralized software solution that allows you to achieve complete HIPAA compliance. We pair you with a dedicated coach to guide you through the process successfully.
Afterwards, the software and your coach will keep you informed on things you need to do to stay compliant. Should you ever experience a breach, we are there to walk you through the breach notification process quickly and easily.