Phishing emails target recipients by posing as trusted entities, with the purpose of accessing the recipient’s email account. Hackers have become sophisticated in drafting such emails, with 90% of cyberattacks originating from phishing emails.
Hackers don’t just impersonate individuals, rather large well-known organizations. Generally the email will reference a recipient’s need to reset a compromised password, prompting them to click on a link. The link will then redirect the recipient to a seemingly trusted site where users are asked to provide their login credentials. The hacker then has the recipient’s login information for whichever company they are posing as.
Vade Secure recently conducted a report to determine phishers’ favorite brands to impersonate, identifying Microsoft as the top brand they use to perpetrate phishing attacks. The report stated, “Over the course of the [last] quarter,” the researchers report, “our AI engine detected a staggering 20,217 unique Microsoft phishing URLs, for an average of more than 222 per day.” This is particularly concerning for the healthcare industry as many use Office 365 to conduct business. Once a hacker has the login credentials for a user’s Microsoft account, they can access their email, and more concerning, their cloud storage.
The report further identified the top 10 brands that phishers impersonate:
- Microsoft
- PayPal
- Netflix
- Bank of America
- Apple
- CIBC
- Amazon
- DHL
- Docusign
How to Recognize Phishing Emails
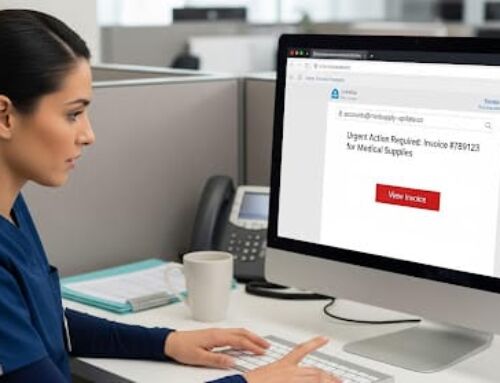
When receiving any email that prompts you to click on a link or provide login credentials, you should be wary. Hackers have become sophisticated in drafting phishing emails, and can often convincingly impersonate trusted entities. As such, it is always best practices to check the email address that the email is sent from. Emails from companies will usually have a dedicated domain which will display as user@companyname. Emails coming from personal email addresses such as [email protected] or [email protected], should not be opened.
Additionally, before clicking on any links, you should hover over the link to ensure that the link display name matches the URL that you will be directed to. If they differ, the email is probably a phishing email and you should not click on the link. When in doubt, always contact the company to make sure that the email is legitimate. However, DO NOT use the contact information provided in the email. Instead, look up the company’s contact information so that you can be sure that you are contacting the legitimate company.