Where data breaches and cyber threats are of constant concern, trust has become a crucial factor for businesses. Clients and customers want to be assured that their sensitive information is in safe hands when they engage with an organization. This is where SOC 2 comes into play.
SOC 2 (Service Organization Control Type 2) is an auditing framework designed to ensure the security, availability, processing integrity, confidentiality, and privacy of customer data. The five trust service criteria for SOC 2 help organizations build trust with their stakeholders.
Security: Safeguarding Against Unauthorized Access
Security is the cornerstone of any reliable system or organization. The first trust principle for SOC 2 focuses on ensuring appropriate measures are in place to secure protected health information (PHI) from unauthorized access or disclosure. It encompasses not only technical safeguards like firewalls and encryption but also policies, procedures, and training that prevent internal threats.
By adhering to the security criterion laid out by the SOC 2 framework, organizations can demonstrate their commitment to protecting client data from potential breaches or attacks, thereby fostering trust among their customers.
Availability: Maintaining Uninterrupted Service
In today’s fast-paced world, downtime can have severe consequences for any business. The availability trust principle for SOC 2 ensures that systems and services are readily available for operation as agreed upon with clients or users.
It involves:
- Robust Infrastructure Planning
- Redundancy Measures
- Disaster Recovery Protocols
- Proactive Monitoring
Organizations complying with the availability criterion demonstrate their dedication to providing reliable services without interruptions or extended periods of unavailability. This reliability builds confidence in clients who rely on continuous access to critical resources.
Processing Integrity: Delivering Accurate & Complete Information
To establish trust among stakeholders, organizations need to maintain accurate records and ensure the integrity of their data processing systems. The processing integrity trust principle of SOC 2 readiness evaluates whether transactions are authorized, complete, accurate, and timely.
By implementing appropriate controls and validation processes, organizations can demonstrate their commitment to delivering reliable information to clients. This promotes transparency and instills confidence as customers know they can rely on accurate records for decision-making.
Confidentiality: Protecting Sensitive Information
Confidentiality is crucial when handling sensitive customer data. Organizations need to have robust measures in place to protect this information from unauthorized disclosure or use. The confidentiality trust principle for SOC 2 evaluates the policies, procedures, and technologies employed to safeguard confidential data.
Companies adhering to the confidentiality criterion assure their clients that their personal or financial information is handled with utmost care and protected against potential breaches. This fosters trust by showing a commitment to privacy and protecting sensitive data from falling into the wrong hands.
Privacy: Complying with Applicable Laws and Regulations
Privacy has gained significant importance with the ever-increasing concerns around data protection and regulations such as HIPAA (Health Insurance Portability and Accountability Act), GDPR (General Data Protection Regulation) or CCPA (California Consumer Privacy Act).
The privacy trust principle for SOC 2 assesses an organization’s compliance with relevant laws and regulations governing the:
- Collection
- Use
- Retention
- Disclosure
- Disposal
of personal information. By demonstrating adherence to privacy requirements, organizations build trust among customers who value their rights to privacy. Compliance with applicable regulations shows a commitment to safeguarding personal information while upholding legal obligations.
The five trust service criteria for SOC 2 – security, availability, processing integrity, confidentiality, and privacy – provide a comprehensive framework for organizations aiming to establish trust with stakeholders. By addressing these principles within their operations and undergoing SOC 2 audits conducted by independent third parties, businesses can showcase their commitment to:
- Protecting client data
- Maintaining secure systems
- Ensuring uninterrupted services
- Delivering accurate information
- Safeguarding sensitive information
- Complying with privacy regulations
Embracing these trust principles not only safeguards organizations against potential risks but also helps establish a strong foundation of trust among clients and customers who rely on their services.
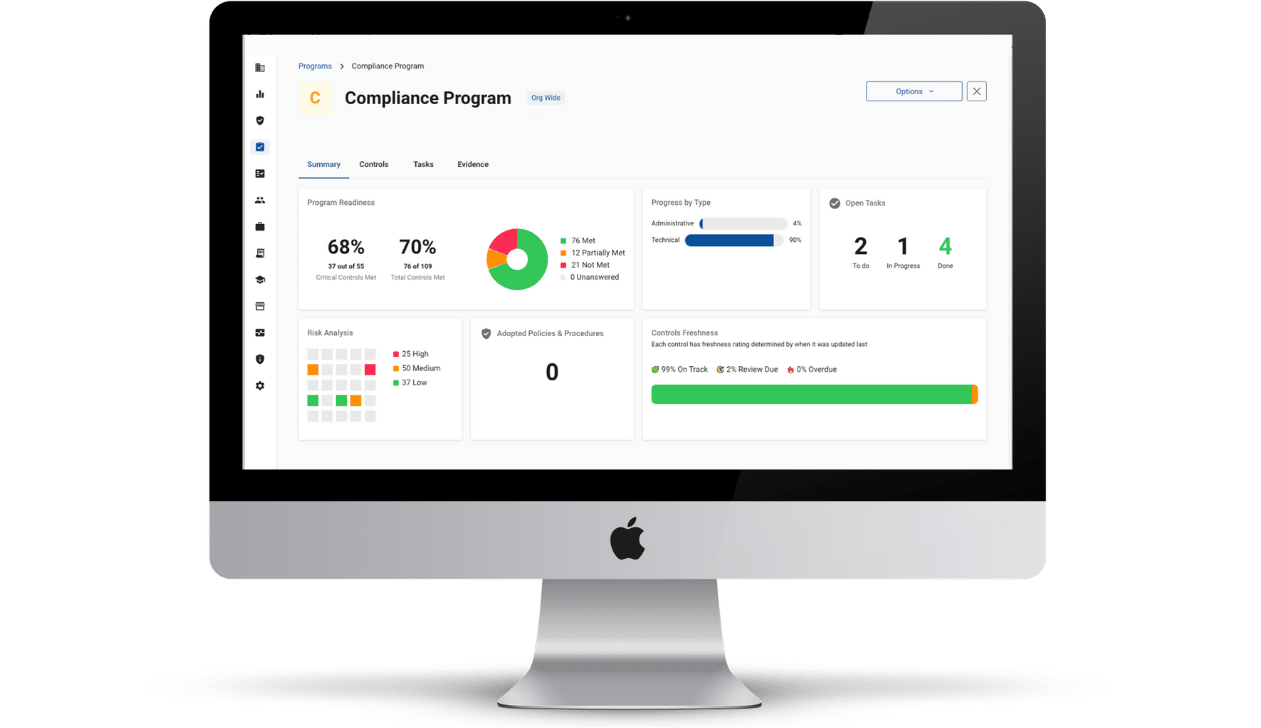
Evaluate your security posture with Compliancy Group’s SOC 2 readiness software. Show your healthcare clients that you take protecting their data seriously using the industry-standard security framework. Get the documentation you need for your CPA to evaluate your SOC 2 status.