What is HIPAA Risk Management?
The HIPAA Security Rule requires that covered entities (health plans, health care clearinghouses, and health care providers who electronically transmit any health information in connection with a HIPAA-related transaction), and business associates (read more about business associates here), implement policies and procedures to prevent, detect, contain, and correct security violations. Implementing these policies and procedures helps to ensure the security of electronic protected health information (ePHI).

One of the policies that must be implemented is a HIPAA risk management policy. A risk management policy is a required administrative safeguard under the HIPAA Security Rule.
HIPAA Risk Management Concepts – Vulnerabilities, Threats, and Risks
To understand what HIPAA risk management is, let’s look at and define three terms: vulnerabilities, threats, and risks.
Vulnerabilities are weaknesses or gaps in an organization’s security program that can be exploited to gain unauthorized access to ePHI. An example of a vulnerability is not having your data encrypted.
Threats are things that can exploit these vulnerabilities and damage or destroy ePHI. Threats include malware, phishing schemes, and viruses.
Risk is the potential for damage or destruction to ePHI as a result of a threat exploiting a vulnerability.
The three terms can now be put together in a single sentence: If your data is not encrypted (a vulnerability), there is a risk your ePHI may be damaged as a result of a malware attack (a threat).
Risk Management Probability and Impact
Every risk has both a probability and an impact.
Risk probability is the chance of a risk occurring. Risk impact is the cost of a risk if it does occur.
Take the example of attending a baseball game. A spectator at the game runs the risk that he or she will spill a soda that he or she purchased. The probability of the risk is not non-existent (especially if the soda-buyer is sitting in a full row and there is only a short distance between the person’s shoes and the end of the step the person is sitting on).
While the probability of the soda spilling isn’t insignificant (let’s call it 10%), the impact – the costs – are not that high. The person who bought the soda will have to purchase another and someone will have to clean the spill.
Let’s slightly change the facts. A foul ball strikes our soda-buyer, hitting him or her in the arm, and causing the soda to spill in the process. The probability of this chain of events actually occurring is pretty low – let’s say, less than one percent. The impact or cost, however, can be significant. As before, costs can include cleaning costs and the costs of a replacement soda. The costs in the foul ball victim hypothetical can be much greater. That person, as a result of being hit in the arm, may break his or her arm. The costs of a broken arm can include surgery and medication, and can also include intangible costs, such as pain and the inability to use the arm for a period of time.
Putting it All Together
A HIPAA risk management plan should contain a risk analysis and a risk mitigation strategy.
The risk analysis is a listing of likely and unlikely risks, with both high and low impacts. In the analysis, risks with both the highest probabilities AND the highest impact are ranked highest on the list, while risks with the lowest probabilities and impacts are ranked lowest (at the bottom).
The HIPAA risk management plan should contain a mitigation (or loss prevention) strategy for each item ranked on the list. A mitigation strategy is a series of steps designed to limit the probability and impact of the risk. If the risk to be guarded against is, for example, a malware attack, the analysis should contain steps designed to minimize the likelihood and impact of the attack.
Once you develop a HIPAA risk management plan, you should share and review the plan with the appropriate employees, so that they will know what is required on their part to successfully implement the plan. You should also periodically review your HIPAA risk management plan to prevent its becoming stale and not reflective of actual risks and costs.
Compliancy Group Simplifies HIPAA Compliance
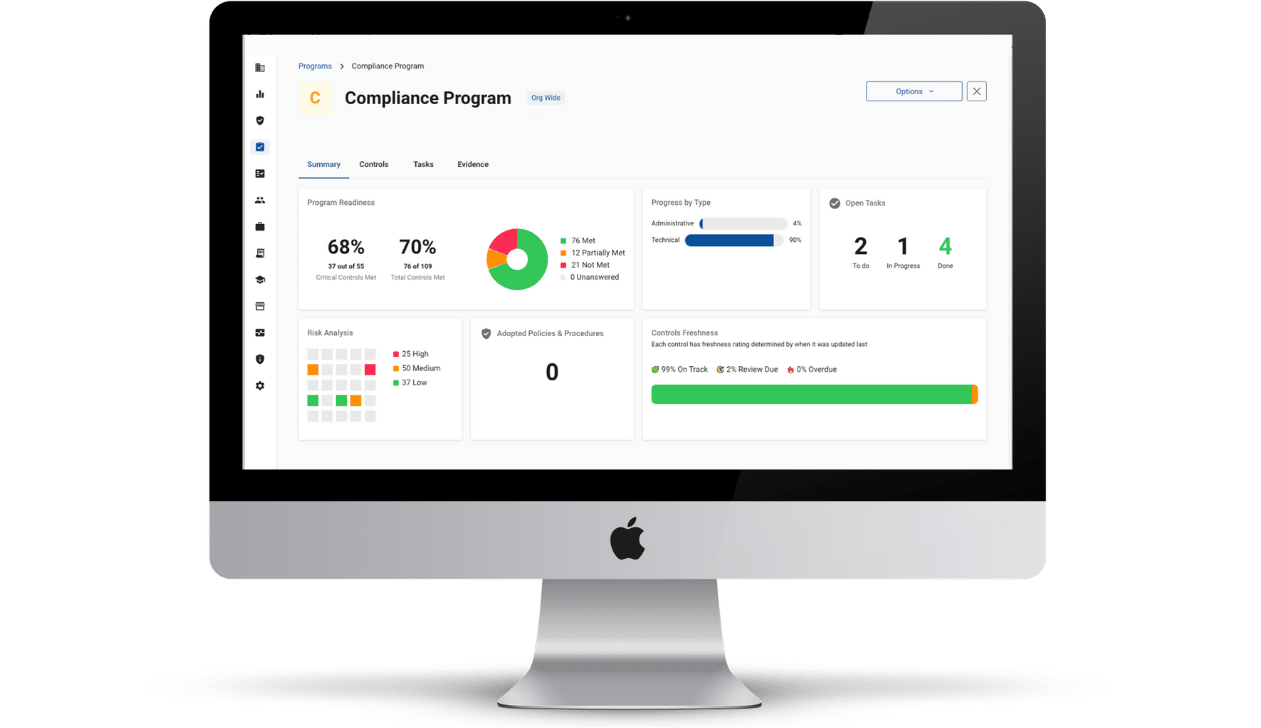
By working with Compliancy Group to address federal HIPAA security standards, covered entities and business associates can address their HIPAA risk management obligations. Developing and reviewing HIPAA risk management plans is required to become HIPAA-compliant.
Our ongoing support and web-based compliance app, The Guard™, gives health care organizations the tools to address HIPAA Security Rule standards so they can get back to confidently running their business.
Find out how Compliancy Group has helped thousands of organizations like yours Achieve, Illustrate, and Maintain their HIPAA compliance!