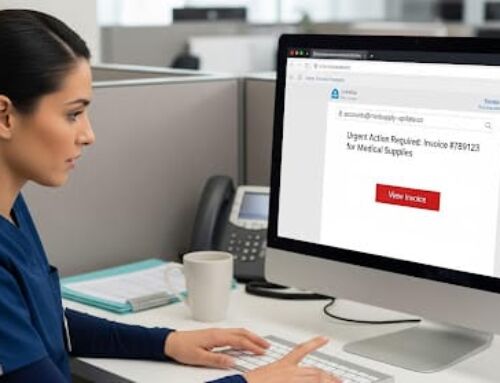
East Central Indiana School Trust (ECIST) is the latest victim of a healthcare phishing attack. A phishing attack occurs when a hacker sends an email, posing as a trusted individual, prompting the recipient to click a malicious link. When the recipient clicks the link, the hacker is able to access their email account, including emails sent and received, email attachments, and address books. They often use the information to perpetuate further attacks.
In this instance, the hacker was only able to access one employee’s email account and the breach was detected a few days after it occurred. The email account in question contained the protected health information (PHI) of 3,259 employees and their dependents. Information such as names of employees and their dependents, date of birth, Social Security numbers, driver’s license numbers, health insurance information, prescription details, and some medical information, was contained in the compromised email account.
Upon detection, ECIST was able to secure the hacked email account and they hired a third-party computer forensics company to investigate. Although the forensics company did not find evidence that the emails containing PHI were opened, they could not rule out unauthorized access. The breach was reported to the Department of Health and Human Services’ (HHS) Office for Civil Rights (OCR) and affected individuals.
Healthcare Phishing Attacks
Healthcare phishing attacks are the most common reason behind healthcare breaches of late. As such, healthcare organizations must ensure that their employees are trained on how to recognize phishing emails, and how to report a suspected incident. Phishing emails can be difficult to detect by design, as hackers can be extremely convincing in mimicking trusted individuals. Employees should always hover over an email address before opening any links to ensure that the email is coming from a trusted user. In addition, links should also be hovered over before opening to verify that the link is directing recipients to a legitimate website. When in doubt, contact the sender directly to ensure that they are the person that sent the email.