Data security has become a paramount concern for organizations of all sizes. With cyber threats rising, businesses are under constant pressure to ensure secure systems and processes. One way to achieve this is by becoming SOC 2 compliant.
What is SOC 2 Compliance?
SOC 2 compliance refers to adhering to the Service Organization Control (SOC) 2 framework, designed specifically for service providers that store customer data in the cloud or process sensitive information. It sets forth a series of criteria for evaluating an organization’s controls related to security, availability, processing integrity, confidentiality, and privacy.
The Difference Between SOC 2 Type 1 and Type 2 Compliance
There are two types of SOC 2 reports – Type 1 and Type 2. Understanding the difference between them is crucial when considering the level of compliance you want to achieve.
- SOC 2 Type 1 Compliance: This report evaluates the design effectiveness of an organization’s controls at a specific point in time. It provides insights into whether control objectives have been adequately developed and implemented.
- SOC 2 Type 2 Compliance: Unlike Type 1, this report assesses both the design and operational effectiveness of controls over a period of time (typically six months or more). It offers a deeper understanding of how well controls are functioning in practice.
Why is SOC 2 Compliance Important?
Maintaining SOC 2 compliance demonstrates a commitment to protecting customers’ data and establishes stakeholder trust. In an era where data breaches can result in devastating consequences such as reputational damage and financial loss, being SOC 2 compliant can be a competitive advantage. It assures clients that their data is handled securely and reduces the risk of potential breaches or unauthorized access.
How to Become SOC 2 Compliant
Achieving SOC 2 compliance requires careful planning, implementation, and continuous monitoring. Here are the essential steps to becoming SOC 2 compliant.
1. Determine Your Scope
Identify the systems, processes, and data that fall under the scope of SOC 2 compliance. This step involves evaluating which trust services categories (security, availability, processing integrity, confidentiality, and privacy) are relevant to your organization.
2. Develop Policies and Procedures
Establish comprehensive policies and procedures that align with the criteria outlined in the SOC 2 framework. These should cover areas such as access controls, incident response protocols, change management, and data classification.
3. Implement Controls
Put in place technical and administrative controls to safeguard customer data effectively. This may include encryption techniques, multi-factor authentication, intrusion detection systems, regular vulnerability assessments, and employee training programs.
4. Conduct Regular Audits
Perform internal audits to assess the effectiveness of controls and identify any gaps or vulnerabilities. These audits help ensure ongoing adherence to SOC 2 requirements while allowing for timely remediation of any issues that arise.
5. Engage an Independent Auditor
Engaging a qualified independent auditor is crucial for obtaining a SOC 2 report. The auditor will evaluate your controls against the applicable trust services criteria and issue an opinion on your compliance efforts.
6. Remediate Identified Issues
Address any deficiencies or weaknesses identified during the auditing process promptly. This may involve revising policies or enhancing control mechanisms to meet SOC 2 standards fully.
7. Maintain Continuous Monitoring
Compliance is not a one-time effort; it requires continuous monitoring of controls to remain effective over time. Regularly review and update policies and procedures as necessary to adapt to evolving cybersecurity threats.
Preparing for SOC 2 Compliance
Becoming SOC 2 compliant is a rigorous but invaluable process for organizations aiming to protect sensitive data and maintain customer trust. By implementing robust security measures, adhering to established frameworks, and undergoing regular audits, businesses can demonstrate their commitment to data protection while gaining a competitive edge in the marketplace. SOC 2 compliance is not only about meeting industry standards; it’s about safeguarding your customers’ information and instilling confidence in your organization’s ability to handle data securely.
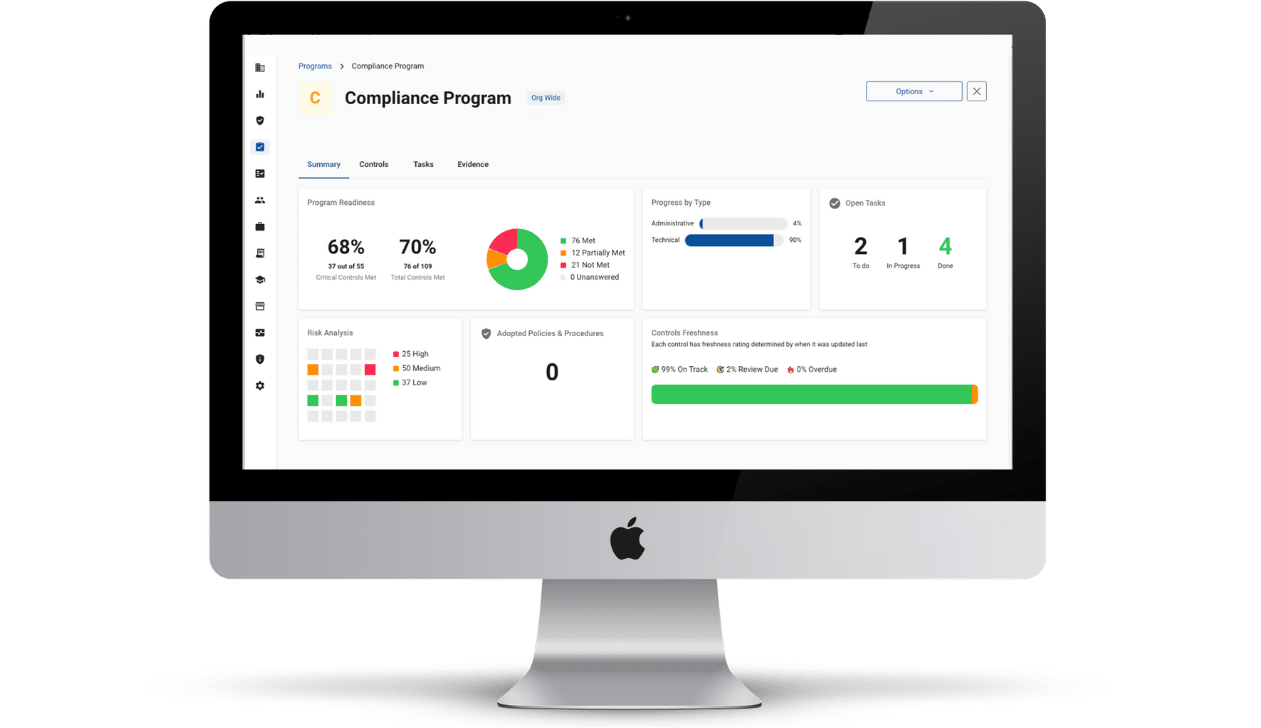
Evaluate your security posture with Compliancy Group’s SOC 2 readiness software. Show your healthcare clients that you take protecting their data seriously using the industry-standard security framework. Get the documentation you need for your CPA to evaluate your SOC 2 status.
- Programs: Guided action items that follow SOC 2 Framework requirements.
- Evidence Collection: Easily generate SOC 2 documentation with automation.
- Eliminate Redundancies: Answer a question once, it’s applied to all compliance standards.