In an era where data breaches and privacy concerns are making headlines regularly, it has become increasingly important for organizations to prioritize protecting sensitive information. For healthcare providers and entities that handle protected health information (PHI), compliance with HIPAA regulations is mandatory and crucial for maintaining patient trust.
One essential component of compliance is conducting a thorough HIPAA privacy risk assessment. We will delve into the significance of HIPAA privacy risk assessments, explore the requirements, provide insights on how to conduct one effectively, and highlight useful tools and templates available.
Understanding the Importance of HIPAA Privacy Risk Assessments
The Health Insurance Portability and Accountability Act (HIPAA) was introduced in 1996 with the primary objective of safeguarding individuals’ medical records and other personal health information. The law established standards for the electronic exchange, privacy, and security of PHI.
Among its provisions, HIPAA requires covered entities such as:
- Hospitals
- Doctors’ Offices
- Health Insurers
- Clearinghouses
to regularly assess potential risks to patients’ confidential information. A comprehensive privacy risk assessment helps organizations identify vulnerabilities within their systems or processes that could potentially compromise patient data.
By identifying these risks proactively, organizations can take appropriate measures to mitigate them before any breach occurs. This ensures compliance with HIPAA regulations and demonstrates a commitment to protecting patients’ privacy rights.
HIPAA Privacy Risk Assessment Requirements: Taking Action the Right Way
Several key elements need to be considered to conduct an effective privacy risk assessment under HIPAA guidelines.
1. Identify Potential Risks
Start by comprehensively reviewing all aspects of your organization’s operations that involve PHI. Look for potential areas where unauthorized access or disclosure could occur, such as:
- Electronic Systems
- Physical Storage Areas
- Communication Channels
- Employee Practices
2. Evaluate Current Security Measures
Assess the existing safeguards and security measures in place to protect PHI. This includes:
- Evaluating Technical Controls
- Administrative Policies
- Physical Safeguards
- Employee Training Programs
3. Document Findings
It is crucial to maintain a record of your risk assessment findings, including:
- Identified Vulnerabilities
- Potential Impacts
- Likelihood of Occurrence
- Level of Risk
4. Develop a Corrective Action Plan
Based on the assessment findings, outline a plan to address any identified risks or vulnerabilities. This could include:
- Implementing Additional Security Measures
- Revising Policies & Procedures
- Enhancing Employee Training Programs
How to Conduct a Privacy Risk Assessment: Making it Manageable
Conducting a privacy risk assessment can be complex; however, breaking it down into manageable steps can help ensure its success. Here is a simplified approach.
1. Define Scope and Objectives
Clearly define the scope of your risk assessment by identifying the systems, processes, and areas within your organization that handle PHI. Set clear objectives for what you aim to achieve through the assessment.
2. Identify Potential Risks
Thoroughly examine all aspects of your organization’s operations involving PHI. Consider both internal and external factors that may pose risks to patient data confidentiality.
3. Assess Current Security Measures
Evaluate existing security controls in place to protect PHI. This includes reviewing technical safeguards like firewalls and encryption protocols, administrative policies such as access control and workforce management, physical safeguards like facility access controls and video surveillance systems, and employee training programs on privacy awareness.
4. Analyze Vulnerabilities
Analyze each identified risk or vulnerability based on its potential impact on patient data confidentiality. Consider the likelihood of occurrence and assign a risk level (low, medium, high) to prioritize mitigation efforts.
5. Develop Mitigation Strategies
Based on the analysis conducted in step four, develop strategies to mitigate identified risks effectively. These strategies should align with HIPAA requirements and best practices for safeguarding PHI.
6. Implement and Monitor
Put your mitigation strategies into action, ensuring appropriate security measures are implemented. Regularly monitor and review the effectiveness of these measures to identify any new risks that may arise over time.
HIPAA Privacy Risk Assessment Template: Streamlining the Process
Many organizations utilize a HIPAA privacy risk assessment template to streamline the process of conducting a privacy risk assessment. This template serves as a standardized framework that guides healthcare professionals through various aspects they must consider when evaluating their security measures.
A well-designed template will typically include sections such as:
- Administrative Safeguards
- Physical Safeguards
- Technical Safeguards
- Workforce Training Requirements
- Business Associate Agreements
- Incident Response Plans
- Breach Notification Protocols
By following this template and answering specific questions within each section, organizations can ensure they cover all necessary areas during their assessment.
Leveraging Technology: HIPAA Privacy Risk Assessment Tools
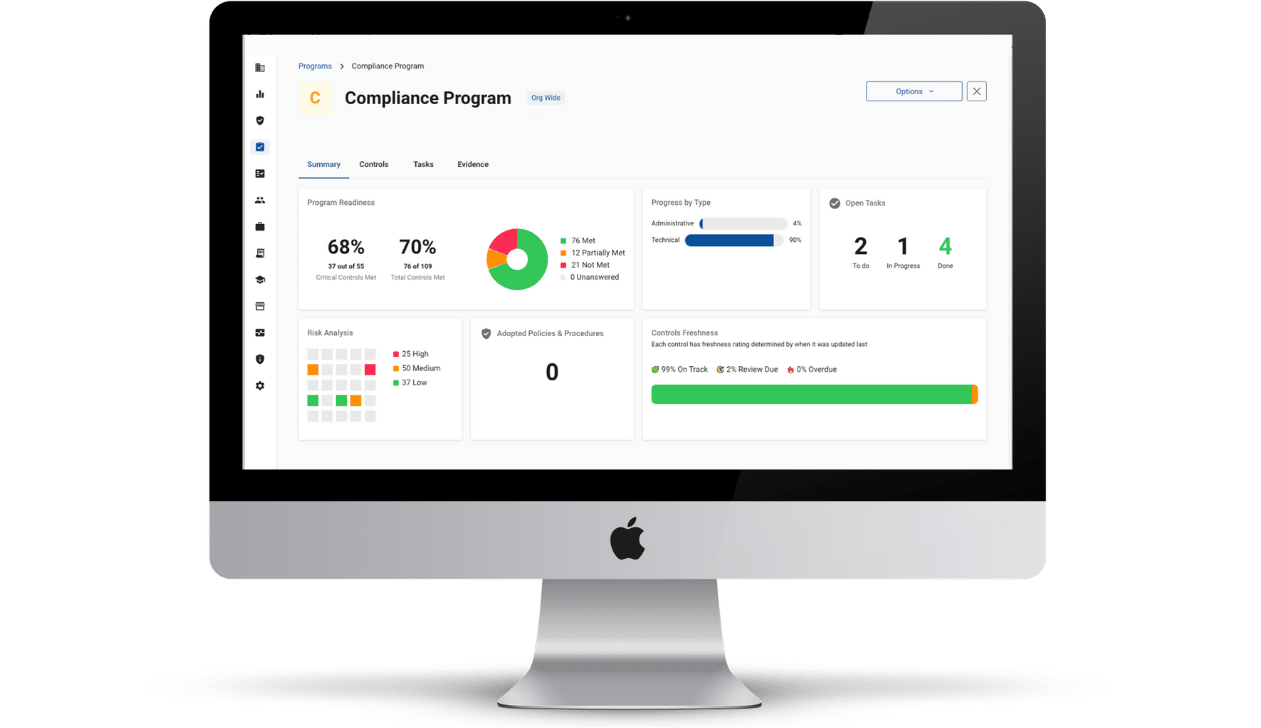
With advancements in technology, numerous tools are now available that can assist organizations in conducting their privacy risk assessments effectively. These tools simplify the process and provide automated features that help track progress and generate reports.
A reliable HIPAA privacy risk assessment tool should be able to identify potential vulnerabilities and suggest appropriate security measures. It should also offer features for monitoring compliance with HIPAA regulations and recommend necessary improvements.
By utilizing templates, tools, and following a structured approach, healthcare organizations can identify potential vulnerabilities and implement robust safeguards to protect electronic protected health information. Regular assessments ensure compliance with HIPAA regulations and demonstrate an unwavering commitment to maintaining patient trust and confidentiality in an increasingly interconnected world.
Compliancy Group’s healthcare compliance software makes it easy to identify risks and mitigate them with corrective actions. Simply answer a series of yes/no questions and your risk profile is automatically generated. Get peace of mind in your compliance with a comprehensive solution!