Business email compromise (BEC) – also known as CEO impersonation – is a favorite crime of Internet con artists because the practice relies on what any con operation requires for success: deception. These criminals target employees with access to company cash. Scammers identify which individuals have this access, and the names of the CEOs for whom they work, the scammer then sends the individuals a seemingly legitimate email requesting a wire transfer. The wire transfer request appears to come from the CEO. The individual reading the request, thinking it is legitimate, ends up sending money to cybercriminals.
In a new twist on this scheme, business email compromise scammers, operating out of Nigeria, have recently been targeting government healthcare agencies, COVID-19 research organizations, and pandemic response organizations, to obtain fraudulent wire transfer payments and spread malware.
When Did Business Email Compromise Scammers Begin Their Attacks?
The latest attacks were detected by Unit 42 of Palo Alto Networks, a cybersecurity researcher. The researchers have attributed these attacks to a cybercriminal group known as SilverTerrier, which has conducted at least 2.1 business email compromise attacks since 2014. In 2019, SilverTerrier’s activity peaked, when, in June, 245,637 attacks were conducted.
How Do Business Email Compromise Scammers Carry Out Their Attacks?
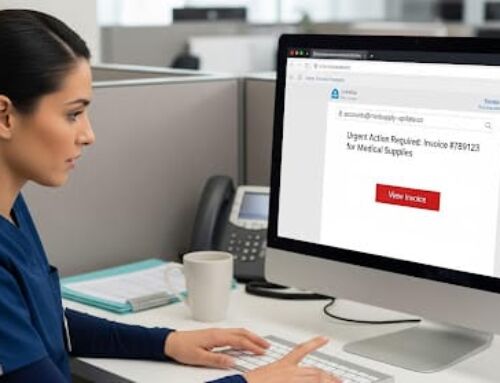
BEC attacks are conducted to obtain fraudulent wire payments. The attacks trick individuals with access to company finances into thinking a scammer’s message to transfer funds is actually a legitimate request from the CEO. To conduct this attack, SilverTerrier uses spear phishing emails. To make the email seem legitimate, the attackers use lures such as fake invoices and payment advice notifications. These techniques trick the email recipients into opening malicious email attachments that install malware. SilverTerrier then uses the malware to steal sensitive information and gain access to bank accounts and payroll systems.
Is your organization secure?
Find out now with our HIPAA compliance checklist!
What Recent Activities Has Unit 42 Detected?
Unit 42 researchers have tracked the activity of three threat actors from the group over the past 3 months. These actors have conducted COVID-19 themed malware campaigns on organizations involved in the national response to COVID-19 in a number of countries. These countries include Australia, Canada, Italy, the United Kingdom, and the United States.
The specific targets of the scammers include government healthcare agencies, local and regional governments, medical publishing companies, research firms, insurance companies, and universities with medical programs and medical centers. To date, the researchers have identified 170 distinct phishing emails, a number of which are related to supplies of face masks and other personal protective equipment.
Since the attacks are mostly conducted by email, the best defense is training for staff to help them identify spear phishing emails and an advanced spam filtering solution to prevent the emails from being delivered to inboxes. Organizations should also continue to promptly apply patches.