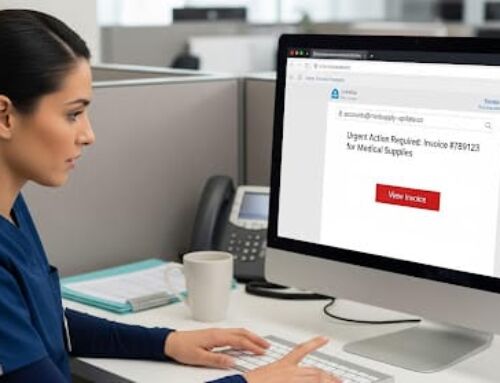
Hackers utilizing phishing attacks disguise themselves as a trusted entity, to send their victims links with malicious content, either through email, text, or instant message. When the receiver clicks the link, hackers are able to gain access to their system. Organizations that are maintaining or transmitting protected health information (PHI) must have safeguards in place to protect their data.
The Department of Health and Human Services (HHS) identifies ten practices organizations should implement to increase their cybersecurity:
- Email protection systems
- Endpoint protection systems
- Access management
- Data protection and loss prevention
- Asset management
- Network management
- Vulnerability management
- Incident response
- Medical device security
- Cybersecurity policies
645,000 Oregonians Affected by Phishing Attacks
Nine employees of Oregon’s Department of Human Services (DHS) clicked on a malicious link contained in a phishing email, compromising the protected health information (PHI) of 645,000 Oregonians. The link allowed the sender to access the employees’ email accounts, including email attachments with reports containing PHI. The exposed data included names, birth dates, addresses, Social Security numbers, personal health information, case numbers, as well as additional information used in DHS programs.
The breach occurred on January 8, 2019 and lasted until January 28, 2019. Employees noticed issues with their computers and notified their employer. The department in conjunction with the Enterprise Security Office Cyber Security team investigated the data breach. They concluded that the data breach was a phishing incident, only affecting the email accounts of the nine individuals who clicked the link.
DHS notified the public on March 21, 2019, once it was confirmed by ID Experts that the compromised data included PHI. In response, ID Experts is offering 12 months of identity theft monitoring and recovery services through MyIDCare. This includes a $1 million insurance reimbursement policy. The department is also sending affected individuals breach notices, along with instructions on how to enroll in the MyIDCare monitoring services. Consumers can also freeze their credit reports, at no cost, through Equifax, Experian, and TransUnion.
Although, DHS trains its staff regularly on how to recognize phishing attacks, employees are still clicking on malicious links. Recognizing phishing emails can protect your organization from data breaches, but encrypting your data is imperative to protecting PHI. This way if you experience a data breach, PHI will be protected.
Navicent Health Phishing Attack Affects 278,016 Individuals
Navicent Health Systems falls victim to a phishing attack, affecting 278,016 individuals. Monroe County Hospital was among those affected by the incidents with 10,970 of their patients’ health information exposed by the breach. Monroe County Hospital was informed of the breach on March 26, 2019. The hospital informed affected patients by mail on May 24.
Hackers gained access to patient information by infiltrating the email accounts of several Navicent Health employees. Exposed information included protected health information (PHI) such as names, birth dates, addresses, Social Security numbers, driver license numbers, medical record numbers, and limited health information. Navicent Health reported the incident to law enforcement in July 2018, but it took forensic investigators 6 months to determine that PHI was compromised. However, it was unclear if attackers viewed or downloaded the PHI.
In a press release Navicent Health stated, “We take our responsibility to safeguard personal information seriously and apologize for any inconvenience or concern this incident might cause. We are committed to taking steps to help prevent something like this from happening again, including evaluating additional platforms for educating staff and reviewing technical controls.” Since the breach, Navicent Health has been working to improve their security with the help of multiple cybersecurity firms.