Data breaches and security threats have become increasingly common, making it crucial for organizations to demonstrate their commitment to protecting sensitive information. SOC 2 certification has emerged as a valuable mechanism companies can utilize to instill trust and confidence in their clients. Let’s delve into the significance of a SOC 2 certification, its process, and why it has become a benchmark for secure data management.
Understanding SOC 2 Certification
SOC 2 certification, also known as System and Organization Controls 2 certification, is an industry-standard framework developed by the American Institute of Certified Public Accountants (AICPA).
It assesses an organization’s ability to manage customer data based on five key trust principles:
- Security
- Availability
- Processing Integrity
- Confidentiality
- Privacy
By obtaining a SOC 2 certification, businesses can provide assurance to their customers that they have implemented robust controls and procedures to protect sensitive information. This certification validates an organization’s commitment to maintaining high standards of security and privacy throughout its operations.
SOC 2 Type 2 Certification
While SOC 2 Type 1 certification assesses an organization’s controls at a specific point in time, SOC 2 Type 2 certification evaluates these controls over a defined period. This type of certification provides greater assurance by demonstrating that controls have been consistently operating effectively over time.
The SOC 2 Type 2 Certification Process
Achieving SOC 2 type 2 certification involves several key steps that companies must follow meticulously. Let’s break down the process.
1. Defining the Scope
Identifying the scope of the assessment, including systems processes and services that will be evaluated for compliance with the trust service principles.
2. Gap Analysis
Conducting an initial assessment to identify any gaps between current practices and SOC 2 requirements. This helps organizations understand areas where improvements are needed.
3. Remediation
Implementing necessary changes to address identified gaps and strengthen organizational control measures.
4. Audit Planning
Collaborating with a certified third-party auditing firm to devise an audit plan tailored to the organization’s specific needs.
5. On-Site Assessment
The auditing firm conducts an on-site review of controls, interviews employees, examines documentation, and tests security protocols to verify compliance with the SOC 2 framework.
6. Reporting
Upon completion of the assessment, a detailed report is generated outlining the findings, control effectiveness, and any recommendations for improvement.
Benefits of SOC 2 Certification
With cyber threats evolving rapidly, businesses face immense pressure to safeguard the data entrusted to them. SOC 2 certification demonstrates an organization’s dedication to maintaining security practices. Here are some reasons why a SOC 2 certificate has gained significant importance.
1. Enhancing Customer Confidence
SOC 2 certification reassures clients that their data is being handled with the utmost care and meets stringent security requirements. It builds trust between organizations and their customers by providing tangible evidence that security measures are in place.
2. Competitive Advantage
Obtaining a SOC 2 certificate sets businesses apart from competitors who may have yet to undergo such rigorous assessments. It gives potential clients peace of mind knowing that they are partnering with a company committed to protecting their valuable information.
3. Compliance with Regulatory Standards
SOC 2 certification aligns organizations with industry regulations and compliance requirements, such as HIPAA. This ensures that businesses are well-prepared to handle customer data following legal obligations.
4. Internal Process Improvements
Going through the SOC 2 certification process compels organizations to assess their existing controls and identify areas for improvement critically. This leads to enhanced internal processes, increased efficiency, and reduced risk of security incidents.
Achieving Success By Obtaining Your SOC 2 Certificate
Remember, obtaining a SOC 2 certificate is not just a one-time achievement; it requires ongoing commitment to maintain and improve security practices. As technology continues to evolve, businesses must adapt their controls to stay ahead of emerging threats. By prioritizing data protection through SOC 2 certification, organizations can establish themselves as beacons of trust and security in the digital age.
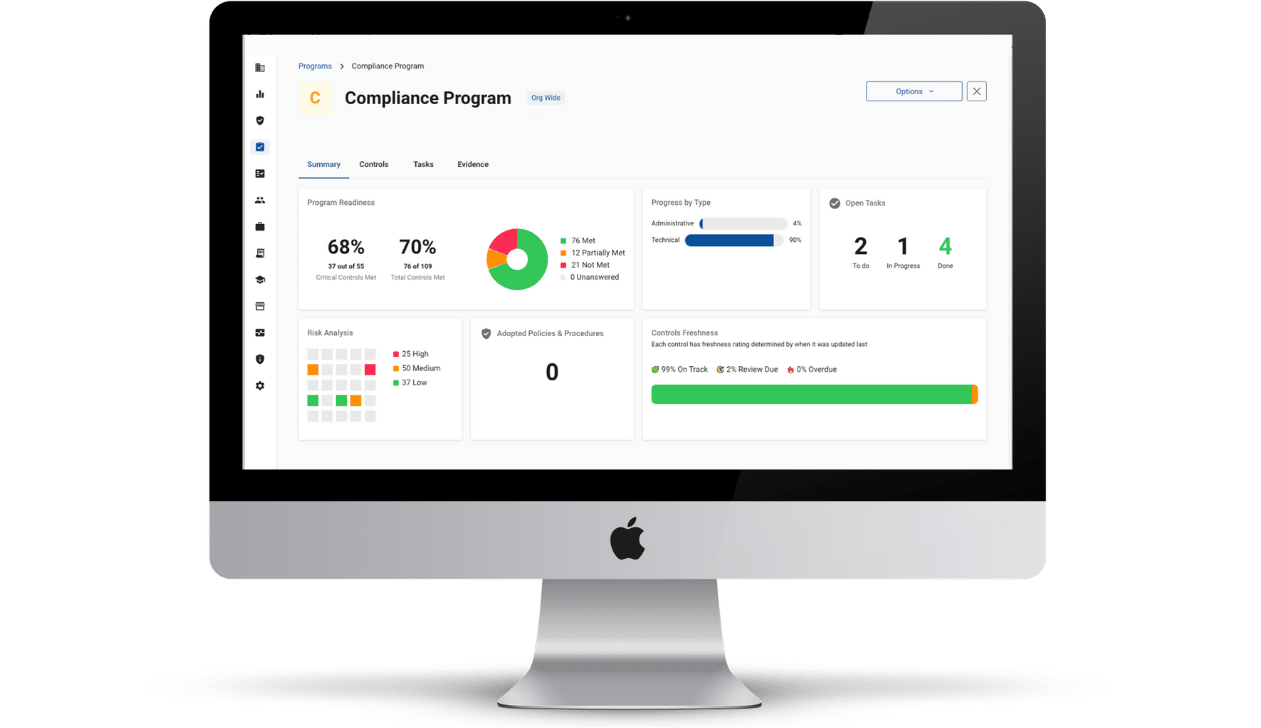
Evaluate your security posture with Compliancy Group’s SOC 2 readiness software. Show your healthcare clients that you take protecting their data seriously using the industry-standard security framework. Get the documentation you need for your CPA to evaluate your SOC 2 status.