Where data breaches and cyber threats are a constant concern, organizations must prioritize the security and privacy of their customers’ information. One way to demonstrate this commitment is by undergoing a SOC 2 audit. A SOC 2 audit is an independent assessment of an organization’s internal controls and processes related to security, availability, processing integrity, confidentiality, and privacy.
Understanding the SOC 2 Audit Process
The SOC 2 audit process involves several steps to evaluate an organization’s adherence to the criteria outlined in the American Institute of Certified Public Accountants (AICPA) Trust Services Criteria. Let’s take a closer look at each stage.
1. Planning
Before commencing the audit, both the auditors and the organization being audited collaborate to establish objectives, scope, timelines, and resource requirements.
2. Examination
During this phase, auditors assess the design and operating effectiveness of controls implemented by the organization. They may review policies, procedures, and documentation, conduct interviews with key personnel, and perform testing activities.
3. Reporting
Once the examination is complete, auditors prepare a comprehensive SOC 2 audit report that outlines their findings. This report is essential for stakeholders to understand an organization’s commitment to data security and compliance.
Key Components of a SOC 2 Audit Report
A well-crafted SOC 2 audit report contains vital information about an organization’s compliance with various trust services criteria. Some key components are as follows.
1. Independent Auditor’s Opinion
This section provides an unbiased evaluation of whether an organization has successfully met all relevant control objectives.
2. Description of System
Here, auditors detail the system or systems under review during the audit process.
3. Control Objectives
Auditors outline specific control objectives established by management to ensure compliance with the AICPA Trust Services Criteria.
4. Control Activities
This section describes the controls used to achieve objectives and safeguard customer data.
5. Test Procedures and Results
Auditors document testing methods employed during the audit, along with the results of their assessments.
SOC 2 Audit Requirements and Compliance
To ensure a successful SOC 2 audit, organizations must meet specific requirements.
1. Establishing Control Objectives
Organizations must define control objectives aligning with the AICPA Trust Services Criteria relevant to their business operations.
2. Implementing Controls
It is crucial for organizations to implement adequate controls to address identified risks and protect sensitive information effectively.
3. Documentation
Maintaining accurate and up-to-date documentation is essential for demonstrating compliance during an audit.
SOC 2 Type 2 Audit: Going Beyond Type 1
While a SOC 2 Type 1 audit evaluates an organization’s controls at a specific point in time, a SOC 2 Type 2 audit provides a more comprehensive assessment. In a SOC 2 Type 2 audit, auditors review the design and operating effectiveness of controls over a specified period, often six months or longer. This extended evaluation allows organizations to consistently showcase their commitment to maintaining strong internal controls.
Using SOC 2 Audit Checklist for Preparation
Organizations can use a SOC 2 audit checklist as a valuable tool for preparing themselves before undergoing an audit. Such checklists typically cover various categories, such as:
- Security management
- Logical access controls
- Data privacy
- Change management processes
- Incident response procedures
- Vendor management
By systematically reviewing each item on the checklist, organizations can identify gaps in their control environment and take corrective actions before the official audit begins.
Preparing for a SOC 2 Audit
In today’s digital world, where trust is paramount, organizations must prioritize data security and compliance. Undergoing a SOC 2 audit demonstrates an organization’s commitment to protecting customer information and provides stakeholders with confidence in its internal controls. By adhering to SOC 2 audit requirements, organizations can foster a culture of trust and security, essential for sustained success in the digital age.
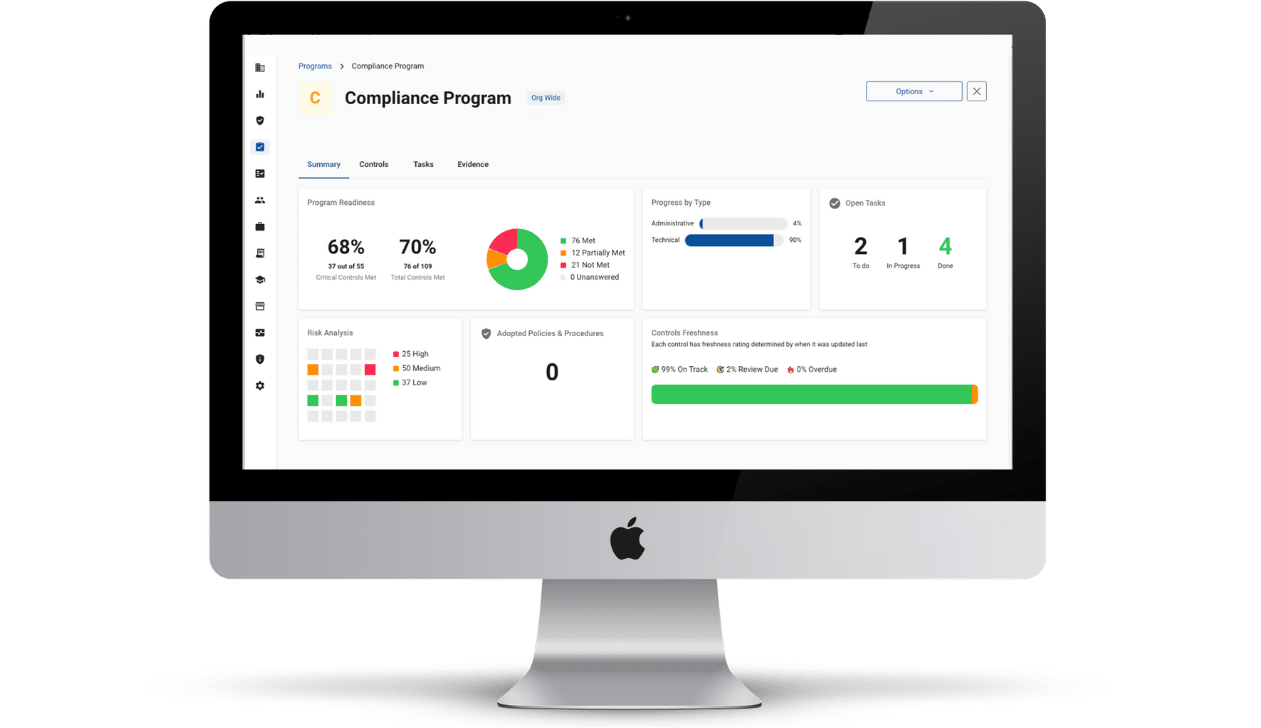
Evaluate your security posture with Compliancy Group’s SOC 2 readiness software. Show your healthcare clients that you take protecting their data seriously using the industry standard security framework. Get the documentation you need for your CPA to evaluate your SOC 2 status.